About
Alhussein A. Abouzeid (Senior Member, IEEE) is a Professor and Department Head of the Department of Electrical, Computer and Systems Engineering at Rensselaer Polytechnic Institute (RPI), Troy, NY, where he has been a faculty member since 2001. He received the B.S. degree with honors in electronics and communications engineering from Cairo University, Egypt, in 1993, and the M.S. and Ph.D. degrees in electrical engineering from the University of Washington, Seattle, in 1999 and 2001, respectively. His research interests are in computer networking, with an emphasis on wireless and mobile systems, including dynamic spectrum access, in-network caching, stochastic network analysis, and IoT.
Dr. Abouzeid has served on three separate appointments as Program Director in the Division of Computer and Networked Systems at the U.S. National Science Foundation (NSF): 2008–2010, 2020–2022 (part-time), and 2022–2025, where he co-directed the Networking Technology and Systems (NeTS) program and co-founded the Enhanced Access to Radio Spectrum (EARS) program. He was the founding director of WiFiUS (2011–2015), an NSF-funded international virtual institute comprising 58 principal investigators from 29 institutions in the US and Finland, and co-founded the Verticals-enabling Intelligent Network Systems (VINES) NSF program. From 2014 to 2019, he held a Finnish Distinguished Professor (FiDiPro) Fellowship from Business Finland, with a visiting appointment as Full Professor at the Center for Wireless Communications, University of Oulu, Finland. Prior to joining RPI, he held engineering positions at Alcatel (now Nokia), Oracle, Hughes Research Labs, and AlliedSignal (now Honeywell).
Dr. Abouzeid has served as Associate Editor for the IEEE Transactions on Wireless Communications, the IEEE Transactions on Mobile Computing, IEEE Wireless Communications Magazine, and Elsevier Computer Networks. He is a recipient of the NSF CAREER Award (2006), the NSF Special Act Award (2025), the Finnish FiDiPro Fellowship (2014), and multiple best paper awards. His research has been supported by NSF and NIH.
Research Areas
Internet of Things & Sensor Networks
Network architectures, protocols, and resource management for large-scale IoT deployments.
View papers →Spectrum Management & Cognitive Radio
Cognitive radio, dynamic spectrum access, tiered spectrum licensing, and spectrum market mechanisms.
View papers →Stochastic Modeling & Queuing
Information-theoretic and queuing-theoretic analysis of network performance, capacity, and delay.
View papers →In-Network Caching
Proactive and retention-aware caching policies for content-centric networks, femtocell and edge networks.
View papers →Vehicular Networks
Traffic flow control, data caching, and multi-hop communications for vehicular network environments.
View papers →Mobile Networks
Medium access, routing, transport, and cross-layer design in cellular, ad hoc, and hybrid wireless systems.
View papers →Representative Projects
- NSF CNS-2007454 — Next Generation Tiered Spectrum Licensing
- VORTeX — Real-time Networking for Virtual Operating Room Environments
- NSF CNS-1422153 — Coexistence and Cooperation in Future Spectrum Sharing Heterogeneous Networks
Teaching
-
ECSE 4660 / 6660Internetworking of ThingsNetwork architectures, protocols, and systems for IoT deployments, including hands-on demos and design projects.
-
ECSE 4670Computer Communication NetworksIntroduction to computer and communication networks: flow control, congestion, routing, TCP/IP, Ethernet, wireless networks, and quantitative modeling.
-
ECSE 6962Mobile & Wireless NetworksAdvanced graduate course on wireless network research. Topics include medium access in cellular, ad hoc, and hybrid networks; routing; flow control; cross-layer design; and cognitive/dynamic spectrum access networks.
-
ECSE 6510Introduction to Stochastic Signals and SystemsRandom processes, spectral analysis, Gaussian and Poisson processes, Markov processes, Wiener/Kalman filtering, and modulation theory.
-
ECSE 4500 / 2500Probability for Engineering ApplicationsAxioms of probability, random variables, distributions, functions of random variables, central limit theorem, and engineering applications.
-
ENGR 2600Modeling and Analysis of UncertaintyUncertainties in engineering measurements, data organization, model development and validation, with emphasis on engineering applications.
-
ECSE 2660Computer Architecture, Networking and Operating SystemsModern computer architecture, processor design, memory hierarchy, layered OS structures, and network protocols.
-
ECSE 6820Queuing Systems and ApplicationsFundamentals of stochastic processes and queuing theory with emphasis on applications to computer systems, communication networks, manufacturing, and service systems.
-
ECSE 2010Electric CircuitsAnalysis of linear electric circuits: resistive and energy-storage elements, controlled sources, op-amps, AC steady state, frequency response, and Laplace transforms.
Research Group
I welcome motivated graduate students interested in pursuing a Ph.D. in wireless networks, network theory, and related areas. Please reach out if you are interested in joining the group.
Current Ph.D. Students

Chibuikem Ezemaduka

Shukai Chen
Ph.D. Alumni — RPI
Dr. Yu Wang

Dr. Gourav Saha

Dr. Samta Shukla

Dr. Teng Liu

Dr. Mehrdad Khaledi

Dr. Dibakar Das

Dr. Di Wang

Dr. Zhenzhen Ye

Dr. Utku Gunay-Acer
Dr. Jing Ai

Dr. Nabhendra Bisnik

Dr. Huaming Wu

Dr. Nianjun Zhou
Ph.D. Alumni — University of Oulu, Finland
Dr. Bidushi Barua
Service
Departmental & University Leadership
- Graduate Program Director, ECSE, Fall 2016 – Spring 2022
- Chair of the Faculty, Faculty Senate, Fall 2018 – Fall 2019
- President, Faculty Senate, Fall 2017 – Spring 2018
- Vice President, Faculty Senate, Fall 2016 – Spring 2017
Journal Editorships
- Associate Editor, IEEE Transactions on Wireless Communications
- Associate Editor, IEEE Transactions on Mobile Computing
- Associate Editor, IEEE Wireless Communications Magazine
- Associate Editor, Elsevier Computer Networks
- Associate Editor, Elsevier Nano Communication Networks (2010–2011)
Conference & Workshop Organization (Selected)
- General Chair, IEEE International Symposium on Dynamic Spectrum Access Networks (DySPAN 2026)
- General Chair, IEEE International Conference on Mobile Ad-Hoc and Smart Systems (MASS 2021)
- TPC Co-Chair, ACM MobiHoc 2020 — a highly selective flagship conference of ACM SIGMobile
- Area Chair, IEEE INFOCOM, 2018–present
- Panel Co-Chair, IEEE SECON 2010, Boston, MA
- TPC Co-Chair, 4th International ICST Conference on Nano-Networks (Nano-Net 2009), Luzern, Switzerland
- Poster Co-Chair, IEEE SECON 2008, San Francisco, CA
- Founding Director, WiFiUS NSF-funded US-Finland virtual institute (2011)
- NSF NeTS Program Co-Director & EARS Program Co-founder (2008–2010)
Technical Program Committees (Selected)
- IEEE INFOCOM (2004, 2005, 2008, 2009, 2010, 2011)
- IEEE SECON (2006, 2007, 2008, 2010)
- IEEE ICC Wireless Networks Symposium (2004, 2008, 2009)
- IEEE GLOBECOM (2005, 2008)
- IEEE WCNC (2005, 2007, 2008)
- ACM MobiCom / MobiHoc (various years)
- IFIP Networking (2007, 2008)
- ACM IWCMC (2006)
Honors & Awards
-
NSF Special Act Award for Outstanding Contributions, July 2025.
"This award acknowledges your exemplary leadership and innovation in advancing cross-sector partnerships and collaborative program development in wireless networking initiatives of national and international importance." - RPI School of Engineering Outstanding Team Award, 2021.
- Best Paper Award, IEEE/IFIP WiOpt 2016. Paper: "On Designing Optimal Memory Damage Aware Caching Policies for Content-Centric Networks."
- IEEE Senior Member, Spring 2015.
-
Finnish Distinguished Professor Fellow (FiDiPro), Tekes Funding Agency for Innovation, January 2014.
A competitive award enabling distinguished international researchers to collaborate with leading Finnish researchers. Includes 5-year funding for 2 PhD students at University of Oulu and summer visit support. - Track Chair Award, IEEE Communications Society, ICCCN 2013, Nassau, Bahamas, July–August 2013.
-
Founder and Co-Director, NSF WiFiUS, 2011–2015.
NSF-funded consortium of 58 principal investigators from 29 institutions in the US and Finland for joint research and education on wireless networks (wifius.org). - Best Paper Award, ACM/SIGMOBILE MobiOpp 2010, Pisa, Italy. Paper: "Random Walks in Time-Graphs."
- Best Paper Runner-Up (Top 3), ACM MSWiM 2008, Vancouver, BC. Paper: "A Unified Model for Joint Throughput-Overhead Analysis of Mobile Ad Hoc Networks."
- Co-Founded NSF EARS Program (Enhanced Access to Radio Spectrum), 2010.
- NSF CAREER Award, 2006. "CAREER: Multiple-Layer Modeling and Design of Wireless Ad Hoc Networks."
- Best Paper Nomination, ICOIN 2003, Jeju Island, Korea. Paper: "Information-Theoretic Bounds for Mobile Ad-Hoc Networks Routing Protocols."
- IEEE GLOBECOM Student Travel Grant, November 2000.
- Yang Research Award Finalist, Best Research Assistant, Electrical Engineering, University of Washington, June 2000.
- Honors Graduate, Cairo University, Faculty of Engineering, June 1993.
K-12 Outreach
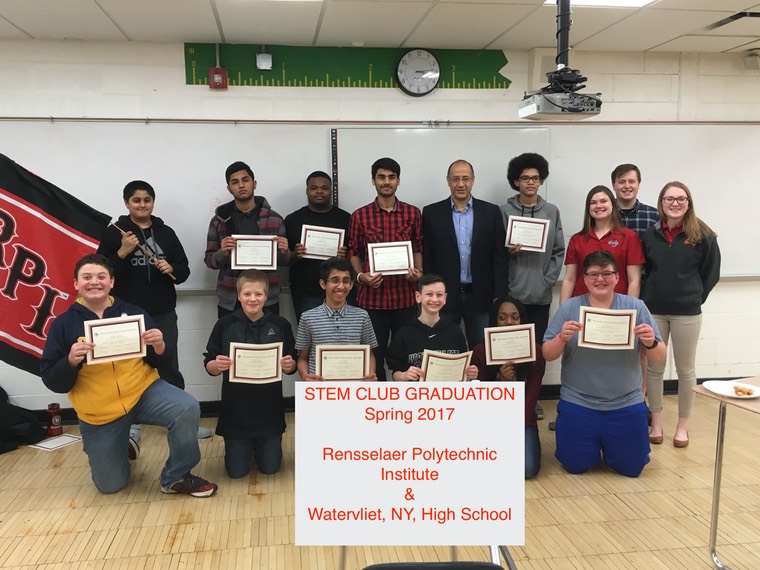
Thanks to NSF funding, I have led a number of outreach activities to high school students at neighborhood schools. Collaborations have included the Rensselaer Ambassadors program, with administrative support from RPI School of Engineering staff (thanks to Elizabeth Herkenham, Director, K-12 Education Outreach, SoE, RPI).
2016–2017 STEM Outreach @ Watervliet High School
Two RPI ECSE undergraduate students, Leslie Chase and Ian Steenstra, designed and delivered a STEM outreach program to Watervliet High School in Spring 2017. They prepared an exciting set of activities during Fall 2016 built around Raspberry Pi and Arduino, to introduce circuits and embedded/mobile computing to students.

Publications
-
Spec-GNN: Spectrum Enforcement Through Graph Neural Networks in Dynamic Spectrum Access Systems.IEEE Transactions on Cognitive Communications and Networking, vol. 12, no. 4, pp. 1070–1085, July 2025.
Abstract
The underlay access mode in dynamic spectrum access (DSA) systems permits secondary users to transmit con- currently with the primary user, provided that the cumulative interference imposed on the primary user does not exceed a set threshold. A spectrum outage is said to have occurred when the interference threshold has been exceeded. To limit the occurrence of an outage, the spectrum sharing policy mandates that all secondary users transmit within set power limits. However, an outage could still occur due to “spectrum violators” who are secondary users that fail to adhere to the spectrum policy, or it could occur due to unforeseen noise within the spectrum environment. In this work, we design an algorithm for detecting and identifying spectrum violators (if any), which we collectively term ”enforcement”. We propose a novel graph neural network (GNN) based algorithm, Spec-GNN, to identify which secondary users, if any, are spectrum violators when an outage occurs. Because of the noise in a communication system, outages can occur even without the presence of violators, and thus a key challenge is to keep the false alarm rate low. Spec-GNN performs by utilizing as input, a graph of the DSA system formed from data collected from monitoring sensors deployed in the environment. Spec-GNN then learns the roles of each secondary user in the graph, allowing it to classify them as violators or not. We extensively evaluate Spec-GNN across diverse settings with varying number of available sensors, secondary users, and violators. The results show that even with low sensor densities, Spec-GNN can achieve accuracy of around 95% with false alarm rates as low as under 0.03 in realistic outage scenarios. We also show that Spec-GNN’s performance is quite robust to the amount of participating secondary users in the DSA system. Even when the number of violators makes up as much as 50% of the secondary users, Spec-GNN is still able to achieve a classification accuracy of close to 92%, while keeping the false alarm rate under 0.04. -
A Beamforming Attack on Deep Learning-Based Spectrum Violator Localization.IEEE Military Communications Conference (MILCOM 2025), Workshop on 6G and Spectrum Security, Los Angeles, CA, October 2025.
Abstract
We investigate the robustness of deep learning- based transmitter localization techniques to an adversarial machine learning (AML) attack in a realistic scenario, where spectrum violators aim to evade localization without falsifying sensor data. In our proposed attack model, violators strategi- cally apply beamforming to produce authentic but deliberately crafted received signal strength (RSS) measurements at sensors, which when processed by the localization model, misleads it. Our evaluation results show that even with modest antenna array sizes, the attack can increase localization error by up to 5 times relative to non-adversarial conditions, and up to 10 times with larger arrays. We also show that the attack remains effective under stringent conditions such as full sensor coverage, achieving up to 3 times higher localization error in such settings. Our results underscore the need for robust defense mechanisms to secure deep learning-based localization systems in wireless spectrum management.
-
Spatially Correlated Placement Policies for Wireless Content Caching Networks.IEEE International Conference on Communications (ICC 2023), Rome, Italy, May–June 2023.
Abstract
We propose a geographic content placement policy for wireless caching networks. This policy, named Joint Caching Policy (JCP), jointly determines the caching strategy across the set of base stations (BSs) to improve the hit probability of an arbitrarily located user in the network versus caching policies where placement is independent and identically distributed across the BSs. To that end, JCP divides the BSs into groups, and executes a joint caching policy for each group, while content placement is independent across the groups. Existing joint caching policies require knowledge of user location to optimize content placement. On the other hand, JCP does not require any information on user location, and it provides a content placement policy that outperforms the one given by Independent Caching Policy (ICP), proposed by Błaszczyszyn and Giovanidis in 2015, under any user location distribution. We prove that the hit probability under JCP is lower bounded by that of ICP. We further propose an extension of JCP, named JCP-OPT, which improves the hit probability over JCP by solving a concave maximization problem, provided that there is side information about the user locations. We validate the performance of JCP and JCP-OPT via numerical evaluations and demonstrate that they can provide up to a 30% gain in hit probability over ICP. -
Privacy-Aware Deep Learning Based Localization of Spectrum Violators.IEEE 20th International Conference on Mobile Ad Hoc and Smart Systems (MASS 2023), pp. 98–106, Toronto, Canada, September 2023.
Abstract
In spectrum sharing environments such as the Cit- izens Broadband Radio Service (CBRS), spectrum “violators” are secondary users that transmit without permission from the spectrum manager and could therefore cause harmful inter- ference to the primary user, such as a radar, through their illegal transmissions. In such systems, it is desirable to detect the geographic locations of such violators without revealing the location, i.e. privacy, of the primary user. In this paper we propose a privacy-aware violator localization algorithm based on deep learning. In this approach, data collected at sensors are processed in a privacy-aware manner using a Generative Adversarial Network (GAN) based algorithm, and relayed to the centralized spectrum manager, e.g., the Spectrum Access System (SAS). The spectrum manager then detects and geographically lo- calizes the violators based on the received data, using an encoder- decoder Convolutional Neural Network (CNN). We evaluate the proposed solution for a CBRS setting and show that it is able to achieve localization error of only 14 meters when using the GAN processed data for localization. Results also show that it achieves reconstruction error of at most 20% at very low Signal-to-Noise (SNR) ratio of 10 dB at a sensor.
-
On the Optimal Duration of Spectrum Leases in Exclusive License Markets With Stochastic Demand.IEEE/ACM Transactions on Networking, 29(3):1060–1073, June 2021.
Abstract
This paper addresses the following question which is of interest in designing efficient exclusive-use spectrum licenses sold through spectrum auctions. Given a system model in which customer demand, revenue, and bids of wireless operators are characterized by stochastic processes and an operator is interested in joining the market only if its expected revenue is above a threshold and the lease duration is below a threshold, what is the optimal lease duration which maximizes the net customer demand served by the wireless operators? Increasing or decreasing lease duration has many competing effects; while shorter lease duration may increase the efficiency of spectrum allocation, longer lease duration may increase market competition by incentivizing more operators to enter the market. We formulate this problem as a two-stage Stackelberg game consisting of the regulator and the wireless operators and design efficient algorithms to find the Stackelberg equilibrium of the entire game. These algorithms can also be used to find the Stackelberg equilibrium under some generalizations of our model. Using these algorithms, we obtain important numerical results and insights that characterize how the optimal lease duration varies with respect to market parameters in order to maximize the spectrum utilization. A few of our numerical results are non-intuitive as they suggest that increasing market competition may not necessarily improve spectrum utilization. To the best of our knowledge, this paper presents the first mathematical approach to optimize the lease duration of spectrum licenses. -
Optimal Spectrum Partitioning and Licensing in Tiered Access Under Stochastic Market Models.IEEE/ACM Transactions on Networking, doi: 10.1109/TNET.2021.3077643, 2021.
Abstract
We consider the problem of partitioning a spectrum band into M channels of equal bandwidth, and then further assigning these M channels into P licensed channels and M−P unlicensed channels. Licensed channels can be accessed both for licensed and opportunistic use following a tiered structure that has a higher priority for licensed use. Unlicensed channels can be accessed only for opportunistic use. We address the following question in this paper. Given a market setup, what values of M and P maximize the net spectrum utilization of the spectrum band? While this problem is fundamental, it is highly relevant practically, e.g., in the context of partitioning the recently proposed Citizens Broadband Radio Service band. If M is too high or too low, it may decrease spectrum utilization due to limited channel capacity or due to wastage of channel capacity, respectively. If P is too high (low), it will not incentivize the wireless operators who are primarily interested in unlicensed channels (licensed channels) to join the market. These tradeoffs are captured in our optimization problem which manifests itself as a two-stage Stackelberg game. We design an algorithm to solve the Stackelberg game and hence find the optimal M and P. The algorithm design also involves an efficient Monte Carlo integrator to evaluate the expected value of the involved random variables like spectrum utilization and operators’ revenue. We also benchmark our algorithms using numerical simulations. -
A Privacy Attack on Coded Caching by Colluding Users.IEEE Communications Letters, 25(9):3001–3005, 2021.
Abstract
Coded caching is beneficial due to its ability to leverage the multicast property of a wireless channel. Under specific network settings, the coded caching scheme has been shown to reveal the user file requests. In prior work, a privacy attack by a single attacker on coded caching was presented. In this letter, we focus on a relatively secure setting whereby only the intended users access the files. Nevertheless, we show that, even in this setting, privacy is compromised if the users are colluding. The time complexity of the attack on a network with <inline-formula> <tex-math notation="LaTeX">$N$ </tex-math></inline-formula> files, <inline-formula> <tex-math notation="LaTeX">$K$ </tex-math></inline-formula> users, and <inline-formula> <tex-math notation="LaTeX">$l \leq K$ </tex-math></inline-formula> colluding users is shown to be in the order of <inline-formula> <tex-math notation="LaTeX">$\sqrt {\ln (N(K-l))}N^{(K-l)/2}$ </tex-math></inline-formula> steps. -
RCP: A Reinforcement Learning-Based Retransmission Control Protocol for Delivery and Latency Sensitive Applications.IEEE International Conference on Computer Communications and Networks (ICCCN 2021), July 2021.
Abstract
This paper presents the design and performance evaluation of a new machine learning-based transport protocol called Reinforcement learning-based retransmission Control Protocol (RCP). Unlike prior transport protocols that aim at either providing guaranteed end-to-end delivery, e.g., TCP, or minimizing the end-to-end delay, e.g., UDP, RCP aims to optimize any achievable combination of these objectives, as specified by an application layer utility function. The utility function in this paper can be quite general, and can capture a combination of delay and packet delivery metrics. RCP can be thought of as an intelligent middle-ground between UDP and TCP, that maps application layer objectives subject to what is learned about the network state. It is window-based like TCP, but retransmissions are decided based on a reinforcement learning algorithm to maximize the application layer utility function. RCP employs a reinforcement learning method, double Q-Learning network, to learn the best strategy in real-time from a history of packet transmission/re-transmission experiences. No assumption on the shape of the utility function is needed. RCP is evaluated under a wide range of network settings, and is found to outperform UDP, TCP, and ARQ for almost all settings. The performance is also evaluated with respect to TCP-friendliness and network stability.
-
Traffic Flow Control in Vehicular Multi-Hop Networks With Data Caching and Infrastructure Support.IEEE/ACM Transactions on Networking, 28(1):376–386, January 2020.
Abstract
This work studies the user equilibrium (UE) state and the system optimal (SO) state in vehicular communication networks that support both V2V and V2I communication. Each user in this network is assumed to make route choice that optimizes a utility function that involves the traditional travel cost and the data communication utility. The overall social cost is minimized when the network is in the SO state. However, the rational and selfish user behavior brings the network to the UE state. It is well known that, in general, the UE state does not necessarily coincide with the SO state. In this paper, we leverage the data communication aspect of the decision making to influence the users' route choices, driving the UE state to the SO state. We provide a guideline for the system operator on how to drive the network towards the SO state using the V2I bandwidth allocation scheme developed in the paper. The model and the proposed algorithm are validated using Veins simulation under IEEE 802.11p protocol. In the simulation, we also show that the system cost can be lowered compared with the UE state if the bandwidth allocation is close to the optimal solution under the proposed algorithm. -
Traffic Flow Control in Vehicular Multi-Hop Networks with Data Caching.IEEE Transactions on Mobile Computing, 19(1):231–244, January 2020.
Abstract
Control of conventional transportation networks aims at bringing the state of the network (e.g., the traffic flows in the network) to the system optimal (SO) state. This optimum is characterized by the minimality of the social cost function, i.e., the total cost of travel (e.g., travel time) of all drivers. On the other hand, drivers are assumed to be rational and selfish, and make their travel decisions (e.g., route choices) to optimize their own travel costs, bringing the state of the network to a user equilibrium (UE). A classic approach to influence users' route choice is using congestion tolls. In this paper, we study the SO and UE of future connected vehicular transportation networks, where users consider both the travel cost and the utility from data communication, when making their travel decisions. We leverage the data communication aspect of the decision making to influence the user route choices, driving the UE state to the SO state. We assume the cache-enabled vehicles can communicate with other vehicles via vehicle-to-vehicle (V2V) connections. We propose an algorithm for calculating the values of the data communication utility that drive the UE to the SO. This result provides a guideline on how the system operator can adjust the parameters of the communication network (e.g., data pricing and bandwidth) to achieve the optimal social cost. We discuss the insights that the results shed on a secondary optimization that the operator can conduct to maximize its own utility without deviating the transportation network state from the SO. We validate the proposed communication model via Veins simulation. The simulation results also show that the system cost can be lowered even if the bandwidth allocation does not exactly match the optimal allocation policy under 802.11p protocol. -
On the Privacy Leakage of Coded Caching.IEEE International Conference on Communications (ICC 2020), Virtual Conference, June 2020.
Abstract
Coded caching, introduced by Maddah-Ali and Niesen, jointly designs content placement and delivery policies that achieve order-optimal transmission rate. We first prove that the coded caching scheme cannot protect the anonymity of network users when an eavesdropper in the network has access to the broadcast channel. Then, a three-stage attack is proposed to estimate users file requests by building an X-D table mapping between server transmissions X and users requests D. For a coded caching network having Nfiles and Kusers, there are NKdifferent demand vectors. We show that the approximate average time complexity of the proposed attack is only a factor of two from the total number of possible demand vectors, while the best case (for the eavesdropper) time complexity is in the order of only NK. Once the X-D table is completely deduced by the eavesdropper, the users seize from having any privacy. Numerical simulations demonstrate that the analytical results for the time complexity of the attack match well with the simulation results. -
Optimal Joint Partitioning and Licensing of Spectrum Bands in Tiered Spectrum Access under Stochastic Market Models.IEEE/IFIP International Symposium on Modeling and Optimization in Mobile, Ad Hoc, and Wireless Networks (WiOPT 2020), Virtual Conference, June 2020.
Abstract
We consider the problem of partitioning a spectrum band into M channels of equal bandwidth, and then further assigning these M channels into P licensed channels and M−P unlicensed channels. Licensed channels can be accessed both for licensed and opportunistic use following a tiered structure that has a higher priority for licensed use. Unlicensed channels can be accessed only for opportunistic use. We address the following question in this paper. Given a market setup, what values of M and P maximize the net spectrum utilization of the spectrum band? While this problem is fundamental, it is highly relevant practically, e.g., in the context of partitioning the recently proposed Citizens Broadband Radio Service band. If M is too high or too low, it may decrease spectrum utilization due to limited channel capacity or due to wastage of channel capacity, respectively. If P is too high (low), it will not incentivize the wireless operators who are primarily interested in unlicensed channels (licensed channels) to join the market. These tradeoffs are captured in our optimization problem which manifests itself as a two-stage Stackelberg game. We design an algorithm to solve the Stackelberg game and hence find the optimal M and P. The algorithm design also involves an efficient Monte Carlo integrator to evaluate the expected value of the involved random variables like spectrum utilization and operators’ revenue. We also benchmark our algorithms using numerical simulations.
-
Proactive Retention-Aware Caching With Multi-Path Routing for Wireless Edge Networks.IEEE Journal on Selected Areas in Communications, 36(6):1286–1299, June 2018.
Abstract
We consider the problem of proactive retention aware caching in a heterogeneous wireless edge network consisting of mobile users accessing content from a server and associated to one or more edge caches. Our goal is to design a caching policy that minimizes the sum of content storage costs and server access costs over two design variables: the retention time of each cached content and the probability that a user routes content requests to each of its associated caches. We develop a model that captures multiple aspects such as cache storage costs and several capabilities of modern wireless technologies, such as server multicast/unicast transmissions, device multi-path routing, and cache access constraints. We formulate the problem of Proactive Retention Routing Optimization (PRRO) as a non-convex, non-linear mixed-integer program. We prove that it is NP-Hard under both multicast/unicast modes – even when the caches have a large capacity and storage costs are linear – and develop greedy algorithms that have provable performance bounds for the case of uncapacitated caches. Finally, we propose heuristics with low computational complexity for the capacitated cache case as well as for the case of convex storage costs. Systematic evaluations based on real-world data demonstrate the effectiveness of our approach, compared to the existing caching schemes. -
On Contract Design for Incentivizing Users in Cooperative Content Delivery With Adverse Selection.IEEE Transactions on Wireless Communications, 17(12):8418–8432, December 2018.
Abstract
Cooperative content delivery using multiple air interfaces (CCDMI) is a powerful solution to mitigate congestion in cellular networks. In CCDMI, the operator distributes content to selected users that further distribute it locally among its nearby users. However, a user that is capable of contributing to CCDMI might act selfishly and refuse to participate. Although the operator can encourage user participation by offering incentives, it has incomplete information about the users’ willingness to participate. In order to overcome this problem of adverse selection in CCDMI, we propose two contract-based methods under information asymmetry. In both methods, the operator designs a performance-based contract set for the users that are capable of local content distribution. Using a mathematical analysis, we show that the optimal contract under information asymmetry achieves close to optimal utility for the users and the operator, compared with the information symmetry case. Moreover, the users with high willingness to participate get positive utility and the users with low willingness get zero utility. Hence, by assigning contracts, the operator can motivate user participation, despite the information asymmetry between them. Our results verify that the proposed methods improve the system performance in terms of the utility of the operator and the users. -
Online Algorithm for Leasing Wireless Channels in a Three-Tier Spectrum Sharing Framework.IEEE/ACM Transactions on Networking, 26(6):2623–2636, November 2018.
Abstract
To meet the ever growing need for wireless spec- trum, the Federal Communication Commision (FCC) intro- duced a spectrum sharing model called the 3-Tier Sharing Framework. In this model, under-utilized federal spectrum will be released for shared use where the highest preference will be given to Tier-1 followed by Tier-2 and then Tier-3. In this paper, we present a model where a wireless operator, who is interested in maximizing its profit, can operate as a Tier-2 and/or a Tier-3 user. Tier-2 is characterized by paid but “almost” guaranteed and interference free channel access while Tier-3 access is free but has lesser guarantee and also faces channel interference. So the operator has to optimally decide between paid but better channel quality and free but degraded channel quality. Also, the operator has to make these decisions without knowing future market parameters like customer demands or channel availability. We use tools from ski-rental literature to design a deterministic online algorithm for leasing channels which does not rely on the knowledge of market statistics. The efficiency of the online algorithm is analyzed by deriving its competitive ratio (CR) and by conducting simulations. The mathematical model for leasing channels is a novel generalization of the classical ski- rental problem. We therefore make fundamental contribution to ski-rental literature which may have diverse applications beyond the problem considered in this paper. -
Optimal Duration of Spectrum Lease: A Mathematical Approach.IEEE International Symposium on Dynamic Spectrum Access Networks (DySPAN 2018), Seoul, Korea, October 2018.
Abstract
It is widely accepted that the lease duration of spectrum bands sold through auctions plays a crucial role in affecting spectrum utilization. Shorter lease duration increases the frequency of spectrum auctions. Within the scenario studied in this paper, frequent spectrum auctions increases the chances of the spectrum bands being allocated to those operators who can utilize it the best. However, if the lease duration is too short it will not incentivize enough operators to join the market and hence lead to lower competition which in turn deteriorates spectrum utilization. In spite of the importance of lease duration in affecting spectrum utilization, there is no formal study dealing with optimizing the duration of a spectrum lease. This paper presents the first mathematical model to study the effect of lease duration on spectrum utilization under certain market scenario. In such a market scenario, revenue of an operator is the measure of its spectrum utilization. Based on our model, we formulate an optimization problem and develop algorithms to solve the optimization problem for two special cases. Using these algorithms, we numerically study how the optimal characteristics vary with different market parameters.
-
Optimal Device Aware Caching.IEEE Transactions on Mobile Computing, 16(7):1994–2007, July 2017.
Abstract
Caches in Content-Centric Networks (CCN) are increasingly adopting flash memory based storage. The current flash cache technology stores all files with the largest possible “expiry date,” i.e., the files are written in the memory so that they are retained for as long as possible. This, however, does not leverage the CCN data characteristics where content is typically short-lived and has a distinct popularity profile. Writing files in a cache using the longest retention time damages the memory device thus reducing its lifetime. However, writing using a small retention time can increase the content retrieval delay, since, at the time a file is requested, the file may already have been expired from the memory. This motivates us to consider a joint optimization wherein we obtain optimal policies for jointly minimizing the content retrieval delay (which is a network-centric objective) and the flash damage (which is a device-centric objective). Caching decisions now not only involve what to cache but also for how long to cache each file. We design provably optimal policies and numerically compare them against prior policies. -
Proactive Retention Aware Caching.IEEE INFOCOM 2017, Atlanta, GA, May 2017.
Abstract
We consider the problem of proactive (i.e. predic- tive) content caching that is aware of the costs of retention of the content in the cache. Prior work on caching (whether proactive or reactive) does not explicitly take into account the storage cost due to the duration of time for which a content is cached. This new problem, which we call retention aware caching, is motivated by two recent technological developments that are described in the paper: cloud storage rental costs and flash memory damage. We consider a hierarchical network consisting of a server connected to a number of cache-enabled nodes, located either at the edge of a network (e.g. base stations) or in the core of a data center. There are two types of network costs: storage cost at the caches and download cost from the server. We formulate the problem of proactive retention aware data caching (PRAC), which minimizes the total cost subject to the node capacity constraints. We first prove that PRAC is NP-Hard in general and then analyze PRAC for two cases: (1) linear storage cost, (2) convex storage cost. We show that PRAC admits efficient polynomial time algorithms when the storage cost is linear in retention times and caches have a large capacity. Furthermore, we derive bounds on the performance of PRAC for the case when the storage cost is a practically motivated convex function. Numerical evaluations demonstrate that PRAC outperforms other state-of-the-art caching policies for a wide range of parameters of interest. -
Traffic Flow Control in Vehicular Communication Networks.American Control Conference (ACC 2017), Seattle, WA, May 2017.
Abstract
Control of conventional transportation networks aims at bringing the state of the network (e.g., the traffic flows in the network) to the system optimal (SO) state. This optimum is characterized by the minimality of the social cost function, i.e., the total cost of travel (e.g., travel time) of all drivers. On the other hand, drivers are assumed to be rational and selfish, and make their travel decisions (e.g., route choices) to optimize their own travel costs, bringing the state of the network to a user equilibrium (UE). In this paper we study the SO and UE of the future connected vehicular transportation network, where users consider the travel cost and the utility from data communication when making their travel decisions. We leverage the data communication aspect of the decision making to influence the user route choices, driving the UE state to the SO. We propose an algorithm for calculating the SO state, and the values of the data communication utility that drive the UE to the SO. This result provides a guideline on how the communication system operator can adjust the parameters of the communication network (e.g., data pricing and bandwidth) to achieve the optimal social cost. We also discuss the insights on a secondary optimization that the operator can conduct to maximize its own utility without deviating the transportation network state from the SO. -
Hold'em Caching: Proactive Retention-Aware Caching with Multi-Path Routing for Wireless Edge Networks.ACM International Symposium on Mobile Ad Hoc Networking and Computing (MobiHoc 2017), Chennai, India, July 2017.
Abstract
We consider the problem of proactive retention aware caching in a heterogeneous wireless edge network consisting of mobile users connected to a server and associated to one or more edge caches. Our goal is to design a caching policy that minimizes the sum of content storage costs and server access transmissions costs over two design variables: the retention time of each cached content and the probability that a user routes content requests to its asso- ciated caches. We develop a model that captures multiple aspects such as cache storage costs and several capabilities of modern wireless technologies, such as server multicast/unicast transmis- sions, device multipath routing, and cache access constraints. We formulate the problem of Proactive Retention Routing Optimiza- tion (PRRO) as a non-convex, non-linear mixed-integer program. We prove that it is NP-Hard under both multicast/unicast modes, even when the caches have a large capacity, and develop a greedy algorithm that has provable performance bounds. Finally, we propose a heuristic for the capacitated cache case that has low computational complexity. Systematic evaluations including real data sets demonstrate the effectiveness of our approach, compared to the existing caching schemes. -
Infrastructure Bandwidth Allocation for Social Welfare Maximization in Future Connected Autonomous Vehicular Networks.ACM CarSys 2017 (Workshop at MobiCom), Snowbird, UT, October 2017.
Abstract
Control of conventional transportation networks aims at bringing the state of the network to the system optimal (SO) state. This optimum is characterized by the minimality of the social cost function, i.e., the total cost of travel of all drivers. On the other hand, drivers are assumed to be rational and selfish, and make their travel decisions to optimize their own travel costs, bringing the state of the network to a user equilibrium (UE). In this paper, we model the behavior of users in the future connected vehicular transportation networks, where users consider both the travel cost and the utility from data communication when making their travel decisions. We divide the users into two groups based on the kind of data network they are using. We leverage the data communication aspect of the decision making to influence the user route choices, driving the UE state to the SO state. We propose a V2I bandwidth allocation scheme, which provides a guideline on how the system operator can adjust the parameters of the communication network to achieve the optimal UE.
-
Future Micro Operators Business Models in 5G.The Business & Management Review, 7(5):143–149, 2016.
Abstract
This paper focuses on creating an approach and discussing the coopetitive business models of Micro Operators (µO) in the indoors/small cell 5G environment. We define the µO as an entity that combines connectivity with specific content services in spatially confined domains and is dependent on appropriate spectrum resources. We review the literature of 5G business models and develop a framework to discuss the exosystemic, competitive and scalability elements of µO business models. Our findings indicate that the µO concept which has a natural role in the small cell/indoor environment can bring significant value added that complements existing communications services. -
Incentivizing Selected Devices to Perform Cooperative Content Delivery: A Carrier Aggregation Based Approach.IEEE Transactions on Wireless Communications, 15(7):5030–5045, July 2016.
Abstract
In a cooperative content distribution (CCD) using multiple interfaces, a smart wireless device receives content from a base station (BS) on its cellular interface, and it broadcasts the same content through another wireless interface, such as WiFi. However, different users can experience different link qualities, and users with slow wireless links can be a bottleneck in terms of CCD performance. To address this problem, we propose a device selection method which leverages multiple interfaces of the selected devices to perform CCD. Our proposed method takes into account the link quality of both primary (cellular) and secondary (WiFi/short-range) interfaces of the devices, and selects the devices with the best link quality for CCD. To analyze the stability of the proposed CCD method against selfish deviators, we model the problem as a repeated CCD game. We show that although the proposed method yields significant gains in terms of energy and frequency carrier savings, it is vulnerable to selfish deviating users. To address this challenge, we propose a carrier aggregation based incentive mechanism. The analytical and simulation results show that the proposed mechanism maximizes individual and network payoffs, and is an equilibrium against unilateral selfish deviations. -
Cooperative Caching in Dynamic Shared Spectrum Networks.IEEE Transactions on Wireless Communications, 15(7):5060–5075, July 2016.
Abstract
This paper considers cooperation between primary and secondary users in shared spectrum radio networks via caching. We first consider a network with one channel shared between a single macro (primary) base-station and multiple small (secondary) base-stations. Secondary base-stations can cache some primary files and thereby satisfy content requests generated from nearby primary users. For this cooperative scenario, we develop two caching and scheduling policies under which the set of primary and secondary request generation rates that can be supported is expanded from the case without cooperation. The first of these algorithms, Fixed Primary Caching Policy (FPCP), provides more gain in the set of supportable primary and secondary request generation rates. However under this algorithm primary packet transmissions from secondary base-stations do not have higher priority of access than that of secondary packets and thus might suffer in terms of delay. In the second algorithm, Variable Primary Caching Policy (VPCP), primary packet transmissions from the secondary base-stations have higher priority of access than that of secondary packets. We find that the set of primary and secondary request generation rate vectors for which all queues in the network are stable under each of these algorithms is greater than that under any non-cooperative algorithm. We conduct extensive simulations to compare the performance of both algorithms against that of an optimal non-cooperative algorithm. Finally, we extend the analysis to a network with multiple channels. -
Competitive Online Algorithm for Leasing Wireless Channels in 3-Tier Sharing Framework.54th Annual Allerton Conference on Communication, Control, and Computing, Monticello, IL, September 2016.
Abstract
To meet the ever growing need for wireless spec- trum, the Federal Communication Commision (FCC) intro- duced a spectrum sharing model called the 3-Tier Sharing Framework. In this model, under-utilized federal spectrum will be released for shared use where the highest preference will be given to Tier-1 followed by Tier-2 and then Tier-3. In this paper, we present a model where a wireless operator, who is interested in maximizing its profit, can operate as a Tier-2 and/or a Tier-3 user. Tier-2 is characterized by paid but “almost” guaranteed and interference free channel access while Tier-3 access is free but has lesser guarantee and also faces channel interference. So the operator has to optimally decide between paid but better channel quality and free but degraded channel quality. Also, the operator has to make these decisions without knowing future market parameters like customer demands or channel availability. We use tools from ski-rental literature to design a deterministic online algorithm for leasing channels which does not rely on the knowledge of market statistics. The efficiency of the online algorithm is analyzed by deriving its competitive ratio (CR) and by conducting simulations. The mathematical model for leasing channels is a novel generalization of the classical ski- rental problem. We therefore make fundamental contribution to ski-rental literature which may have diverse applications beyond the problem considered in this paper. -
Mobility-Aware Centralized D2D Caching Networks.54th Annual Allerton Conference on Communication, Control, and Computing, Monticello, IL, September 2016.
Abstract
The increase in demand for spectrum-based ser- vices forms a bottleneck in wireless networks. Device-to-Device (D2D) caching networks tackle this problem by exploiting users behavior predictability and the possibility of sharing data between them to alleviate network congestion. Usually, network congestion occurs at certain times of the day and in some popular locations. Consequently, the information about user’s demand alone is not enough. Capturing mobility statistics allows Service Providers (SPs) to enhance their caching strategies. In this work, we introduce a mobility-aware centralized D2D caching network where a SP harnesses users demand and mobility statistics to minimize the incurred service cost through an optimal caching policy. However, the complexity of the optimal caching policy grows exponentially with the number of users. Therefore, we discuss a greedy caching algorithm which has a polynomial order complexity. We also use this greedy algorithm to establish upper and lower bounds on the proactive service gain achieved by the optimal caching policy. -
On Designing Optimal Memory Damage Aware Caching Policies for Content-Centric Networks. Best Paper AwardIEEE/IFIP WiOpt 2016, Phoenix, AZ, May 2016.
Abstract
Caches in Content-Centric Networks (CCN) are increasingly adopting flash memory based storage owing to its efficiency. The current flash cache technology stores all files with the largest possible “expiry date,” i.e., the files are written in the memory so that they are retained for as long as possible. This, however, does not suit the CCN data characteristics where contents are typically short-lived and have a distinct popularity profile. Writing files in cache using the longest retention time damages the flash memory thus reducing the flash lifetime. However, writing using a small retention time can increase the content retrieval delay, since, at the time a file is requested, the file may already have been expired from the memory. This motivates us to propose a joint optimization wherein we obtain optimal policies for jointly minimizing the content retrieval delay (which is a network-centric objective) and the flash damage (which is a device centric objective). Caching decisions now not only involve what to cache and where to cache but also for how long is each file cached. The optimality of our policies are shown analytically, and are compared against prior policies using simulations. -
Content Placement and Service Scheduling in Femtocell Caching Networks.IEEE GLOBECOM 2016, Washington D.C., December 2016.
Abstract
This work considers the joint problem of content placement and service scheduling in femtocell caching networks, to maximize the traffic volume served from the cache. The problem is modeled as a Markov decision process. We combine the Edmonds-Karp algorithm and the marginal allocation algorithm to develop an efficient centralized policy called Infinite CAche-filling (ICA), which can get arbitrarily close to optimal asymptotically as the estimation time window increases. We also design a randomized algorithm called Infinite CAche-filling with Probabilistic scheduling (ICAP) that takes into consideration the femtocells service capability due to interference or multiplexing techniques. We derive a lower bound on the expected discounted hit count of ICAP. We also derive an upper bound on the probability that the performance of ICAP degrades from this expected value. Numerical results show that ICAP scales well and converges relatively fast in response to request pattern changes. -
Hybrid Memory Allocation for Content-Centric Networking.IEEE GLOBECOM 2016, Washington D.C., December 2016.
Abstract
In this work, we study the problem of allocating two types of memory, which have different access speeds, to a set of routers in a single content-centric network. Total network delay is adopted as the performance metric. We first formulate the allocation problem and show that it is NP-hard. Then we prove that this problem is monotone submodular with a matroid constraint. Hence, we are able to derive a guaranteed (1-1/e)-approximation solution when the network is originally stable. We consider tree-structured networks with variable hierarchies under the widely used En-route caching assumption. Simulation results show that the developed algorithm performs well compared to the optimal solution, and only a limited fraction of nodes becomes hybrid regardless of the network size. To the best of our knowledge, this is the first theoretical work on quantitative analysis and algorithm development for hybrid memory allocation for content- centric networking (CCN). -
Optimal Bidding in Repeated Wireless Spectrum Auctions with Budget Constraints.IEEE GLOBECOM 2016, Washington D.C., December 2016.
Abstract
Small operators who take part in secondary wireless spectrum markets typically have strict budget limits. In this paper, we study the bidding problem of a budget constrained operator in repeated secondary spectrum auctions. In existing truthful auctions, truthful bidding is the optimal strategy of a bidder. However, budget limits impact bidding behaviors and make bidding decisions complicated, since bidders may behave differently to avoid running out of money. We formulate the problem as a dynamic auction game between operators, where knowledge of other operators is limited due to the distributed nature of wireless networks/markets. We first present a Markov Decision Process (MDP) formulation of the problem and charac- terize the optimal bidding strategy of an operator, provided that opponents’ bids are i.i.d. Next, we generalize the formulation to a Markov game that, in conjunction with model-free reinforcement learning approaches, enables an operator to make inferences about its opponents based on local observations. Finally, we present a fully distributed learning-based bidding algorithm which relies only on local information. Our numerical results show that our proposed learning-based bidding results in a better utility than truthful bidding.
-
Dynamic Spectrum Sharing Auction with Time-Evolving Channel Qualities.IEEE Transactions on Wireless Communications, 14(11):5900–5912, 2015.
Abstract
Spectrum auction is considered a suitable approach to efficiently allocate spectrum among unlicensed users. In a typical spectrum auction, Secondary Users (SUs) bid to buy spectrum bands from a Primary Owner (PO) who acts as the auctioneer. Existing spectrum auctions assume that SUs have static and known values for the channels. However, in many real world settings, the SUs do not know the exact value of channel access at first, but they learn it and adapt it over time. In this paper, we study spectrum auctions in a dynamic setting where SUs can change their valuations based on their experiences with the channel quality. We propose ADAPTIVE, a dynAmic inDex Auction for sPectrum sharing with TIme-evolving ValuEs that maximizes the social welfare of the SUs. ADAPTIVE is based on multi-armed bandit models where for each user an allocation index is independently calculated in polynomial time. Then we generalize ADAPTIVE to Multi-ADAPTIVE that auctions multiple channels at each time. We provide a sufficient condition under which Multi-ADAPTIVE achieves the maximum social welfare. Both ADAPTIVE and Multi-ADAPTIVE have some desired economic properties that are formally proven in the analysis. Also, we provide a numerical performance comparison between our proposed mechanisms and the well known static auctions, namely the Vickrey second price auction and the VCG mechanism. -
Spatial-Temporal Queuing Theoretic Modeling of Opportunistic Multi-Hop Wireless Networks With and Without Cooperation.IEEE Transactions on Wireless Communications, 14(9):5209–5224, 2015.
Abstract
In this paper, we characterize the average end-to-end delay in an opportunistic multi-hop secondary cognitive radio network overlaid with a primary multi-hop network. Nodes in both networks use random medium access control (MAC) scheme with exponentially distributed back-off. We first model the network as a two-class priority queuing network and use queuing-theoretic approximation techniques to obtain a set of relations involving the mean and second moments of the inter-arrival time and service time of packets at a secondary node. Then, applying these parameters to an equivalent open single-class G/G/1-queuing network, we obtain expressions for the average end- to-end delay of a packet in the secondary network using a diffusion approximation. Next we extend the analysis to a case where secondary nodes cooperatively relay primary packets so as to improve their own transmission opportunities. The mathematical results are validated against extensive simulations. -
Network-Layer Scheduling and Relaying in Cooperative Spectrum Sharing Networks.IEEE Transactions on Wireless Communications, 14(8):4597–4613, 2015.
Abstract
This work considers network-layer cooperation in spectrum sharing networks whereby the secondary users can relay primary users’ packets, in return for more favorable spectrum access rules. Under this cooperative scheme, the paper investigates whether, and under what conditions, the primary and secondary networks can be stabilized without explicit knowledge of the packet arrival rates. We consider a primary packet generation process wherein constant amounts of bit arrive in every time-slot from upper- layers of the primary transmitter. These bits are arranged into a primary packet once sufficient bits have been accumulated. For this primary packet-generation model we develop a relaying and scheduling algorithm using Lyapunov drift techniques that does not require knowledge of packet arrival rates. Aguaranteed stability region consisting of packet generation rates is also constructed, for which the network can be stabilized under this algorithm. The set of secondary packet arrival rate vectors for which the network can be stabilized do not decrease under cooperation when the primary packet generation September 8, 2014 DRAFT 2 rate is lower than what can be maximally supported without cooperation. For higher primary packet generation rates the algorithm stabilizes the network for a non-empty set of secondary packet arrival rate vectors. -
Cooperative Caching for Shared Spectrum Networks.IEEE International Conference on Communications (ICC 2015), London, UK, June 2015.
Abstract
This paper considers cooperation between primary and secondary users in shared spectrum radio networks via caching. A network consisting of a single macro (primary) base-station and multiple small (secondary) base-stations is considered. Secondary base-stations can cache some primary files and thereby satisfy content-requests generated from nearby primary users. For this cooperative scenario, we develop two caching and scheduling policies under which the set of primary and secondary request generation rates that can be supported is expanded from the case without cooperation. The first of these algorithms provide maximum gain in the set of supportable primary and secondary request generation rates. However under this algorithm primary packet transmissions from secondary base-stations do not have higher priority of access than that of secondary packets. As a result, we propose another suboptimal algorithm wherein primary file transmissions from secondary base-stations have high priority of access than that of secondary files. Extensive simulations are conducted to compare the performance of both algorithms with that of a non-cooperative algorithm that is optimal, with respect to set of supportable request generation rates, among all non-cooperative policies. -
Optimal Reserve Prices for Auction-Based Spectrum Sharing.Sixth Nordic Workshop on System & Network Optimization for Wireless (SNOW 2015), Geilo, Norway, March 2015.
-
Weak State versus Strong State: An Analysis of a Probabilistic State Mechanism for Dynamic Networks.Wireless Networks, 20:639–654, 2014.
Abstract
Network protocols coordinate their decision making using information about entities in remote loca- tions. Such information is provided by state entries. To remain valid, the state information needs to be refreshed via control messages. When it refers to a dynamic entity, the state has to be refreshed at a high rate to prevent it frombecoming stale. In capacity constrained networks, this may deteriorate the overall performance of the network. The concept of weak state has been proposed as a remedy to this problem in the context of routing in mobile ad-hoc networks. Weak state is characterized by probabilistic semantics and local refreshes as opposed to strong statethat is interpreted as absolute truth. A measure of the probability that the state remains valid, i.e. confidence , accompanies the state. The confidence is decayed in time to adapt to dynamism and to capture the uncertainty in the state information. This way, weak state remains valid without explicit state refresh messages. We evaluate theconsistency of weak state and strong state using two notions of distortion. Pure distortion measures the averagedifference between the actual value of the entity and thevalue that is provided by the remote state. Informed dis- tortion captures both this difference and the effect ofconfidence value on state consistency. Using a mathemat- ical analysis and simulations, we show that weak state reduces the distortion values when it provides informationabout highly dynamic entities and/or it is utilized for pro- tocols that is required to incur a low amount of overhead. -
Delay Analysis of Multihop Cognitive Radio Networks Using Network of Virtual Priority Queues.IEEE Wireless Communications and Networking Conference (WCNC 2014), Istanbul, Turkey, April 2014.
Abstract
In this paper, we characterize the average end-to-end delay and maximum achievable per-node throughput in an opportunistic secondary cognitive radio network co-existing with a primary network where both networks consist of static nodes that use random medium access schemes. Assuming an ideal sensing mechanism, we first model the secondary network as a two-class priority queuing network and use queuing approximation techniques to obtain a set of relations involving the mean and second moments of the inter-arrival time and service-time of packets at a secondary node. Then, utilizing these parameters in an equivalent open G/G/1 queuing network, we obtain closed form expressions for average end-to-end delay of a packet in the secondary network and the maximum achievable throughput of a secondary node. The results are validated against extensive simulations. -
ADAPTIVE: A Dynamic Index Auction for Spectrum Sharing with Time-Evolving Values.IEEE/IFIP WiOpt 2014, Hammamet, Tunisia, May 2014.
Abstract
Spectrum auction is considered a suitable approach to efficiently allocate spectrum among unlicensed users. In atypical spectrum auction, Secondary Users (SUs) bid to buy spectrum bands from a Primary Owner (PO) who acts as the auctioneer . Existing spectrum auctions assume that SUs havestatic and known values for the channels. However, in manyreal world settings, SUs do not know the exact value of channel access at first, but they learn it over time. In this paper, we study spectrum auctions in a dynamic setting where SUs can changetheir valuations based on their experiences with the channel. Wepropose ADAPTIVE, a dynAmic inDex Auction for sPectrum sharing with TIme-evolving ValuEs that maximizes the social welfare of the SUs. ADAPTIVE is based on multi-armed banditmodels where for each user an allocation index is independentlycalculated in polynomial time. ADAPTIVE has some desired economic properties that are formally proven in the analysis. Also, we provide a numerical performance comparison betweenADAPTIVE and the well known Vickrey second price auction as a representative of static auctions. -
Opportunistic Scheduling and Relaying in a Cooperative Cognitive Network.IEEE/IFIP WiOpt 2014, Hammamet, Tunisia, May 2014.
Abstract
This paper considers network-layer cooperation in cognitive radio networks whereby secondary users may be allowed to relay primary user’s packets. Under this cooperative scheme, the paper investigates whether, and under what conditions, the primary and secondary networks can be stabilized without explicit knowledge of the arrival- rates. We consider a deterministic and periodic primary packet arrival process and develop a relaying and scheduling algorithm using Lyapunov drift techniques that does not require explicit knowledge of primary and secondary packet arrival rates. The algorithm is then shown to stabilize the transmission queues in the network for all secondary packet arrival rates that lie in the interior of a certain region. The region includes all secondary arrival-rate vectors that can be supported when the secondary nodes do not cooperate. Furthermore, when the primary data arrival-rate is greater than what could have been supported without relays but less than what can be maximally supported with relays, the algorithm stabilizes the network for a non-empty set of secondary arrival-rate vectors. The significance of these results is that they show that properly designed cooperation may result in a win-win scenario for both primary and secondary users (and not just for the primary user). Finally we extend our analysis to the case of a deterministic but aperiodic primary packet arrival process.
-
Auction-Based Spectrum Sharing in Cognitive Radio Networks with Heterogeneous Channels.Information Theory and Applications Workshop (ITA 2013), San Diego, CA, February 2013.
Abstract
Cognitive radio is a novel communication paradigm that can significantly improve spectrum utilization by allowing the cognitive radio users to dynamically utilize the licensed spectrum. To achieve this, studying efficient spectrum allocation mechanisms is imperative. In this paper, we consider a cognitive radio network consisting of a primary spectrum owner (PO), multiple primary users (PU) and multiple secondary users (SU). We design an auction-based spectrum sharing mechanism where the SUs bid to buy spectrum bands from the PO who acts as the auctioneer, selling idle spectrum bands to make a profit. Existing auction mechanisms assume that all the channels are identical. However, we consider a more general and more realistic case where channels have different qualities. Also, we allow SUs to express their preferences for each channel separately. That is, each SU submits a vector of bids, one for each channel. The proposed auction mechanism results in efficient allocation that maximizes SUs' valuations, and it has desired economic properties that we formally prove in the analysis. In addition, numerical results show performance improvements in terms of social welfare, SUs' utilities and PO's revenue, compared to the case of identical channels. -
A Reserve Price Auction for Spectrum Sharing with Heterogeneous Channels.IEEE International Conference on Computer Communication Networks (ICCCN 2013), Nassau, Bahamas, July–August 2013.
Abstract
Cognitive radio is a novel communication paradigm that can significantly improve spectrum utilization by allowing the cognitive radio users to dynamically utilize the licensed spectrum. To achieve this, studying efficient spectrum allocation mechanisms is imperative. In this paper, we consider a cognitive radio network consisting of a primary spectrum owner (PO), multiple primary users (PU) and multiple secondary users (SU). We propose a reserve price auction mechanism for spectrum sharing in cognitive radio networks where the SUs bid to buy spectrum bands from the PO who acts as the auctioneer, selling idle spectrum bands to make a profit. Unlike most existing auction mechanisms that assume identical channels, we consider a more general and more realistic case where channels have different qualities. Also, SUs are allowed to express their preferences for each channel separately. That is, each SU submits a vector of bids, one for each channel. In addition, reservation prices that are proportional to channel qualities are imposed by the PO. The proposed auction mechanism results in efficient allocation that maximizes SUs' valuations subject to reserve price constraints, and it has desired economic properties that we formally prove in the analysis. Numerical results show performance improvements compared to the case of reserve price auction with identical channels and the case of having no reservation prices. -
Opportunistic Scheduling and Relaying in a Cooperative Cognitive Network.51st Annual Allerton Conference on Communication, Control, and Computing, Monticello, IL, October 2013.
Abstract
This paper considers network-layer cooperation in cognitive radio networks whereby secondary users may be allowed to relay primary user’s packets. Under this cooperative scheme, the paper investigates whether, and under what conditions, the primary and secondary networks can be stabilized without explicit knowledge of the arrival- rates. We consider a deterministic and periodic primary packet arrival process and develop a relaying and scheduling algorithm using Lyapunov drift techniques that does not require explicit knowledge of primary and secondary packet arrival rates. The algorithm is then shown to stabilize the transmission queues in the network for all secondary packet arrival rates that lie in the interior of a certain region. The region includes all secondary arrival-rate vectors that can be supported when the secondary nodes do not cooperate. Furthermore, when the primary data arrival-rate is greater than what could have been supported without relays but less than what can be maximally supported with relays, the algorithm stabilizes the network for a non-empty set of secondary arrival-rate vectors. The significance of these results is that they show that properly designed cooperation may result in a win-win scenario for both primary and secondary users (and not just for the primary user). Finally we extend our analysis to the case of a deterministic but aperiodic primary packet arrival process. -
A Reserve Price Auction for Spectrum Sharing in Cognitive Radio Networks with Heterogeneous Channels.Fourth Nordic Workshop on System and Network Optimization for Wireless (SNOW 2013), Kittilä, Finland, April 2013.
-
On the Cost of Knowledge of Mobility in Dynamic Networks: An Information-Theoretic Approach.IEEE Transactions on Mobile Computing, 11(6):995–1006, June 2012.
Abstract
In this paper, we extend an information-theoretic approach for characterizing the minimum cost of tracking the motion state information, such as locations and velocities, of nodes in dynamic networks. A rate-distortion formulation is proposed to solve this minimum-cost motion-tracking problem, where the minimum cost is the minimum information rate required to identify the network state at a sequence of tracking time instants within a certain distortion bound. The formulation is applicable to various mobility models, distortion criteria, and stochastic sequences of tracking time instants and hence is general. Under Brownian motion and Gauss-Markov mobility models, we evaluate lower bounds on the information rate of tracking the motion state information of nodes, where the motion state of a node is 1) the node’s locations only, or 2) both its locations and velocities. We apply the obtained results to analyze the geographic routing overhead in mobile ad hoc networks. We present the minimum overhead incurred by maintaining the geographic information of nodes in terms of node mobility, packet arrival process, and distortion bounds. This leads to precise characterizations of the observation that given certain state-distortion allowance, protocols aimed at tracking motion state information may not scale beyond a certain level of node mobility. 1I NTRODUCTION INthis paper, we study communication networks whose state keeps changing over time. Here, the state information of a network m
-
Geographic Protocol Information and Capacity Deficit in Mobile Wireless Ad Hoc Networks.IEEE Transactions on Information Theory, 57(8):5133–5150, August 2011.
Abstract
Overheads incurred by network protocols diminish the capacity available for relaying useful data in a dynamic com-munications network. Discovering lower bounds on the amount ofprotocol overhead incurred is important for the development ofefficient network protocols and for characterizing the effective ca- pacity available for network users. This paper presents an infor-mation-theoretic framework for characterizing the minimum pro-tocol overheads incurred for maintaining location information ina network with mobile nodes. Specifically, the minimum overheadproblem is formulated as a rate-distortion problem. The formu- lation may be applied to networks with arbitrary traffic arrival and location service schemes. Lower bounds are derived for theminimum overheads incurred for maintaining the location of thenodes and consistent neighborhood information in terms of nodemobility and packet arrival processes. This leads to a characteri-zation of the deficit caused by the protocol overheads on the overalltransport capacity. -
Throughput and Delay Analysis for Hybrid Radio-Frequency and Free-Space-Optical (RF/FSO) Networks.Wireless Networks, 17(4):877–892, May 2011.
Abstract
In this paper the per-node throughput and end- to-end delay of randomly deployed (i.e. ad-hoc) hybrid radio frequency - free space optics (RF/FSO) networks arestudied. The hybrid RF/FSO network consists of an RF ad hoc network of nnodes, f(n) of them, termed ‘super nodes’, are equipped with an additional FSO transceiver withtransmission range s(n). Every RF and FSO transceiver is able to transmit at a maximum data rate of W 1and W2 bits/sec, respectively. An upper bound on the per node throughput capacity is derived. In order to prove that this upper bound is achievable, a hybrid routing scheme is designed whereby the data traffic is divided into twoclasses and assigned different forwarding strategies. The capacity improvement with the support of FSO nodes is evaluated and compared against the corresponding resultsfor pure RF wireless networks. Under optimal through- put scaling, the scaling of average end-to-end delay is derived. A significant gain in throughput capacityand a notable reduction in delay will be achieved if fðnÞ¼X 1 sðnÞffiffiffiffiffiffiffi n lognq /C1W1 W2/C18/C19 . Furthermore, it is found that for fixed W1,f(n) and nwhere f(n)\n, there is no capacity incentive to increase the FSO data rate beyond a critical value. In addition, both throughput and delay can achieve linear scaling by properly adjusting the FSO transmissionrange and the number of FSO nodes. -
Connectivity in Time-Graphs.Pervasive and Mobile Computing, 7(2):160–171, April 2011.
Abstract
Dynamic networks are characterized by topologies that vary with time and are represented by time-graphs. The notion of connectivity in time-graphs is fundamentally different from that in static graphs. End-to-end connectivity is achieved opportunistically by the store–carry-forward paradigm if the network is so sparse that source–destination pairs are usually not connected by complete paths. In static graphs, it is well known that the network connectivity is tied to the spectral gap of the underlying adjacency matrix of the topology: if the gap is large, the network is well connected. In this paper, a similar metric is investigated for time-graphs. To this end, a time-graph is represented by a 3-mode reachability tensor which indicates whether a node is reachable from another node in t steps. To evaluate connectivity, we consider the expected hitting time of a random walk, and the time it takes for epidemic routing to infect all vertices. Observations from an extensive set of simulations show that the correlation between the second singular value of the matrix obtained by unfolding the reachability tensor and these indicators is very significant. -
Optimal Stochastic Location Updates in Mobile Ad Hoc Networks.IEEE Transactions on Mobile Computing, 10(5):638–652, May 2011.
Abstract
We consider the location service in a mobile ad-hoc network (MANET), where each node needs to maintain its location information by 1) frequently updating its location information within its neighboring region, which is called neighborhood update (NU), and 2) occasionally updating its location information to certain distributed location server in the network, which is called location server update (LSU). The trade off between the operation costs in location updates and the performance losses of the target application due to location inaccuracies (i.e., application costs) imposes a crucial question for nodes to decide the optimal strategy to update their location information, where the optimality is in the sense of minimizing the overall costs. In this paper, we develop a stochastic sequential decision framework to analyze this problem. Under a Markovian mobility model, the location update decision problem is modeled as a Markov Decision Process (MDP). We first investigate the monotonicity properties of optimal NU and LSU operations with respect to location inaccuracies under a general cost setting. Then, given a separable cost structure, we show that the location update decisions of NU and LSU can be independently carried out without loss of optimality, i.e., a separation property. From the discovered separation property of the problem structure and the monotonicity properties of optimal actions, we find that 1) there always exists asimple optimal threshold -based update rule for LSU operations; 2) for NU operations, an optimal threshold-based update rule exists in a low-mobility scenario. In the case that no a priori knowledge of the MDP model is available, we also introduce a practical model-freelearning approach to find a near-optimal solution for the problem. -
Layered Sequential Decision Policies for Cross-Layer Design of Wireless Ad Hoc Networks.IEEE International Conference on Computer Communications and Networks (ICCCN 2011), Hawaii, USA, July–August 2011.
Abstract
In order to adapt to the time-varying nature of wireless channels, various channel-adaptive schemes have been proposed to exploit inherent spatial diversity in wireless ad hoc networks where there are usually alternateforwarding nodes available at a given forwarding node. However, existing schemes along this line are designed based on heuristics, implying room for performance en-hancement. Thereby, to seek a theoretical foundation for improving spatial diversity gain, we formulate the selection of the next-hop relay as a sequential decision problem and derive a general “Optimal Stopping Relaying (OSR)” framework for designing such s patial-diversity schemes. As a particular example, assuming Rayleigh fading channels, we implement an OSR strategy to optimize information efficiency (IE) in a protocol stack consisting of GreedyPerimeter Stateless Routing (GPSR) and IEEE 802.11 MAC protocols. We present an analysis of the algorithm for a single node. In addition, we perform extensive simulations (using QualNet) to evaluate the end-to-end performance of the proposed forwarding strategy. Theresults demonstrate the superiority of OSR over other existing schemes.
-
Weak State Routing for Large-Scale Dynamic Networks.IEEE/ACM Transactions on Networking, 18(5):1450–1463, October 2010.
Abstract
Routing in communication networks involves the indirection from a persistent name (or ID) to a locator and delivering packets based upon the locator. In a large-scale, highly dynamic network, the ID-to-locator mappings are both large in number, and change often. Traditional routing protocols require high overhead to keep these indirections up-to-date. In this paper, we propose Weak State Routing (WSR), a routing mechanism for large-scale highly dynamic networks. WSR's novelty is that it uses random directional walks biased occasionally by weak indirection state information in intermediate nodes. The indirection state information is weak, i.e. interpreted not as absolute truth, but as probabilistic hints. Nodes only have partial information about the region a destination node is likely to be. This method allows us to aggregate information about a number of remote locations in a geographic region. In other words, the state information maps a set-of-IDs to a geographical region. The intermediate nodes receiving the random walk use a method similar to longest-prefix-match in order to prioritize their mappings to decide how to bias and forward the random walk. WSR can also be viewed as an unstructured distributed hashing technique. WSR displays good rare-object recall with scalability properties similar to structured DHTs, albeit with more tolerance to dynamism and without constraining the degree distribution of the underlying network. Through simulations, we show that WSR offers a high packet delivery ratio, more than 98%. The control packet overhead incurred in the network scales as O(N) for N-node networks. The number of mappings stored in the network appears to scale as $\Theta(N^{3/2})$. We compare WSR with Dynamic Source Routing (DSR) and geographic forwarding (GPSR) combined with Grid Location Service (GLS). Our results indicate that WSR delivers more packets with less overhead at the cost of increased path length. -
A Synchronization Design for UWB-Based Wireless Multimedia Systems.IEEE Transactions on Broadcasting, 56(2):211–225, June 2010.
Abstract
Multi-band orthogonal frequency-division multi- plexing (MB-OFDM) ultra-wideband (UWB) technology offerslarge throughput, low latency and has been adopted in wirelessaudio/video (A V) network products. The complexity and powerconsumption, however, are still major hurdles for the technologyto be widely adopted. In this paper, we propose a unified synchro- nizer design targeted for MB-OFDM transceiver that achieves high performance with low implementation complexity. The keycomponent of the proposed synchronizer is a parallel auto-corre- lator structure in which multiple ACF units are instantiated andtheir outputs are shared by functional blocks in the synchronizer, including preamble signal detection, time-frequency code identi-fication, symbol timing, carrier frequency offset estimation andframe synchronization. This common structure not only reducesthe hardware cost but also minimizes the number of operations inthe functional blocks in the synchronizer as the results of a largeportion of computation can be shared among different functionalblocks. To mitigate the effect of narrowband interference (NBI)on UWB systems, we also propose a low-complexity ACF-basedfrequency detector to facilitate the design of (adaptive) notch filterin analog/digital domain. The theoretical analysis and simulationshow that the performance of the proposed design is close tooptimal, while the complexity is significantly reduced comparedto existing work. -
A Unified Model for Joint Throughput-Overhead Analysis of Random Access Mobile Ad Hoc Networks.Computer Networks, 54(4):573–588, March 2010.
Abstract
We develop an analytical framework to study the through- put and routing overhead for proactive and reactive rout- ing strategies in random access mobile ad hoc networks. To characterize the coexistence of the routing control traffic and data traffic, we model the interaction as a multi-class queue model at each node, where the aggregate control traffic and data traffic are two different classes of customers of the queue. We investigate the scaling property of the through- put, maximum mobility degree supported by the network and mobility-induced throughput deficiencies, under both classes of routing strategies. The proposed analytical model can be extended to incorporate various optimization tech- niques in routing. We present one exemplary technique and discuss its impacts on the scaling properties of throughput and routing overhead. The connection between the derived throughput result and some well-known network throughput capacity results in the literature is also addressed. Categories andSubjectDescriptors C.4 [Performance of Systems ]: Modeling techniques; C.2.2 [Network Protocols ]: routing protocols GeneralTerms Performance, Theory -
On the Cost of Knowledge of Mobility in Dynamic Networks.IEEE INFOCOM 2010 Mini-Conference, San Diego, CA, March 2010.
Abstract
In this paper, we extend an information-theoretic approach for characterizing the minimum cost of tracking the motion state information, such as locations and velocities, of nodes in dynamic networks. A rate-distortion formulation is proposed to solve this minimum-cost motion-tracking problem, where the minimum cost is the minimum information rate required to identify the network state at a sequence of tracking time instants within a certain distortion bound. The formulation is applicable to various mobility models, distortion criteria, and stochastic sequences of tracking time instants and hence is general. Under Brownian motion and Gauss-Markov mobility models, we evaluate lower bounds on the information rate of tracking the motion state information of nodes, where the motion state of a node is 1) the node’s locations only, or 2) both its locations and velocities. We apply the obtained results to analyze the geographic routing overhead in mobile ad hoc networks. We present the minimum overhead incurred by maintaining the geographic information of nodes in terms of node mobility, packet arrival process, and distortion bounds. This leads to precise characterizations of the observation that given certain state-distortion allowance, protocols aimed at tracking motion state information may not scale beyond a certain level of node mobility. 1I NTRODUCTION INthis paper, we study communication networks whose state keeps changing over time. Here, the state information of a network m -
RPL Based Routing for Advanced Metering Infrastructure in Smart Grid.72nd IEEE Vehicular Technology Conference (VTC Fall 2010), Ottawa, Canada, September 2010.
Abstract
In this paper, we present a routing protocol design and implementation for the Advanced Metering Infrastructure (AMI) in Smart Grid. The proposed protocol implementation is based on the framework of the IPv6 Routing Protocol for Low Power and Lossy Networks (RPL), which is proposed by IETF and currently still in its design phase. RPL is based on the idea of maintaining a directed acyclic graph (DAG) structure for the network. We provide a practical implementation of RPL with a number of proper modifications so as to fit into the AMI structure and meet stringent requirements enforced by the AMI. In particular, we propose a novel DAG rank computation method and a reverse path recording mechanism, which enables real-time automated meter reading and real-time remote utility management in the AMI. Our proposed routing protocol design for AMI networks is validated through extensive simulations. -
Random Walks in Time-Graphs. Best Paper AwardSecond ACM/SIGMOBILE International Workshop on Mobile Opportunistic Networking (MobiOpp 2010), Pisa, Italy, February 2010.
-
Optimal Stochastic Policies for Distributed Data Aggregation in Wireless Sensor Networks.IEEE/ACM Transactions on Networking, 17(5):1494–1507, October 2009.
Abstract
We consider the scenario of distributed data aggregation in wireless sensor networks, where each sensor can obtain and estimate the information of the whole sensing field through local data exchange and aggregation. The intrinsic trade-off between energy and delay in aggregation operations imposes a crucial question on nodes to decide optimal instants for forwarding their samples. The samples could be composed of the information from their own sensor readings or an aggregation of information with other samples forwarded from neighboring nodes. By considering the randomness of the sample arrival instants and the uncertainty of the availability of the multiaccess communication channel due to the asynchronous nature of information exchange among neighboring nodes, we propose a decision process model to analyze this problem and determine the optimal decision policies at nodes with local information. We show that, once the statistics of the sample arrival and the availability of the channel satisfy certain conditions, there exist optimal control-limit type policies which are easy to implement in practice. In the case that the required conditions are not satisfied, we provide two learning algorithms to solve a finite-state approximation model of the decision problem. Simulations on a practical distributed data aggregation scenario demonstrate the effectiveness of the developed policies, which can also achieve a desired energy-delay tradeoff. -
Information Theoretic Analysis of Proactive Routing Overhead in Mobile Ad Hoc Networks.IEEE Transactions on Information Theory, 55(10):4608–4625, October 2009.
Abstract
This paper considers basic bounds on the overhead of link-state protocols in mobile ad hoc networks. Hierarchical protocols are known for their good scalability proper- ties, and hence this paper considers a two-level hierarchical protocol. In such protocols, nodes need to keep track of shortest path information, link states and cluster mem- bership. Two types of overheads are considered; the memory needed to store routing- related information, including link-states and cluster membership, and the messages that need to be exchanged to keep track of the changes in the network. Memory over- head is important practically for dimensioning network nodes, while message overhead is important since it reduces the effective capacity of the network to carry user data (vis-a-vis control data). The scalability properties of the routing overhead are analyzed for different modes of network scaling. Practical implications, such as optimal cluster size, average/fixed memory requirement and routing protocol parameter selections are discussed. 1Nianjun Zhou is with IBM, 294 Route 100, Somers, NY 10589; This work was conducted as part of his Ph.D. thesis work at RPI, Troy NY; Tel: (914) 843-3180; e-mail: jzhou@us.ibm.com Alhussein A. Abouzeid is with the Department of Electrical, Computer and Systems Engineering, Rens- selaer Polytechnic Institute, Troy, New York. This work was supported by National Science Foundation grants No. 322956 and 546402. Initial work has appeared in ISIT’2003 symposium and INFOCOM’2005 conference. Correspondence Author: A.A. Abouzeid; 110 Eighth St, JEC-6038, Troy NY 12180; Tel: (518)276-6534; Fax: (518)276-4403; email: abouzeid@ecse.rpi.edu. -
Queuing Network Models for Delay Analysis of Multihop Wireless Ad Hoc Networks.Ad Hoc Networks, 7(1):79–97, January 2009.
Abstract
In this paper we analyze the average end-to-end delay and maximum achievable per-node throughput in random access multihop wireless ad hoc networks with stationary nodes. We present an analytical model that takes into account the number of nodes, the random packet arrival process, the extent of locality of traffic, and the back off and collision avoidance mechanisms of random access MAC. We model random access multihop wireless networks as open G/G/1 queuing networks and use the diffusion approximation in order to evaluate closed form expressions for the average end-to-end delay. The mean service time of nodes is evaluated and used to obtain the maximum achievable per-node throughput. The analytical results obtained here from the queuing network analysis are discussed with regard to similarities and differences from the well established information-theoretic results on throughput and delay scaling laws in ad hoc networks. We also investigate the extent of deviation of delay and throughput in a real world network from the analytical results presented in this paper. We conduct extensive simulations in order to verify the analytical results and also compare them against NS-2 simulations -
Opportunistic Spectrum Access Based on a Constrained Multi-Armed Bandit Formulation.IEEE Journal of Communications and Networks, 11(2):134–147, April 2009.
Abstract
Tracking and exploiting instantaneous spectrum opportuni ties are fundamental challenges in op- portunistic spectrum access (OSA) in presence of the bursty traffic of primary users and the limited spectrum sensing capability of secondary users. In order to take advantage of the history of spectrum sensing and access decisions, a sequential decision framew ork is widely used to design optimal policies. However, many existing schemes, based on a partially observ ed Markov decision process (POMDP) framework, reveal that optimal policies are non-stationar y in nature which renders them difficult to calculate and implement. Therefore, we pursue stationary O SA policies, which are thereby suboptimal yet low-complexity instead, with many practical factors in mind, such as spectrum sensing errors and a priori unknown statistical spectrum knowledge. First, wit h an approximation on channel evolution, we formulate OSA in a multi-armed bandit (MAB) framework. As a r esult, the optimal policy is specified by the well-knownGittins indexrule, wherethe channelwith the largestGittins index is always selected. Then we derive closed-form formulas and design a reinforcem ent learning algorithm to calculate Gittins indices, depending on whether the Markovian channel parame ters are available a priori or not. Finally, we demonstrate the superiority of our scheme over other exis ting schemes in terms of the trade-off between complexity and optimality via extensive simulatio ns. The authors are with Department of Electrical, Computer and Systems Engineering, Rensselaer Polytechnic Institute, T roy, New York 12180. Email: {aij, abouza }@rpi.edu. July 8, 2008 DRAFT -
An Evaluation of Weak State Mechanism Design for Indirection in Dynamic Networks.IEEE INFOCOM 2009, Rio de Janeiro, Brazil, April 2009.
Abstract
State signaling and maintenance mechanisms play crucial roles in communication network protocols. State is used to facilitate indirections in protocols such as routing. De sign approaches for traditional state signaling mechanisms hav e been categorized into soft and hard state. In both approaches, th e state is deterministic. Hence, we call both as having strong state semantics, or more crisply, refer to them as strong state. If the state tracks entities with dynamic nature, strong state rap idly becomes invalidated and needs to be refreshed explicitly th rough control packets. In this paper, we evaluate the recently pro posed weak state [1]. Weak state is a generalization of soft state that is characterized by probabilistic semantics and local update s. It is interpreted as a probabilistic hint and not absolute truth. Weak state also contains the confidence in the state value, which is a measure of the probability that the state remains valid. Th e confidence or the state semantics is decayed locally without the need for explicit state update traffic traversing the networ k. The local updates also help the protocol use better estimates fo r the state value. We define two metrics, pure distortion and informed distortion, to evaluate the consistency of the weak state pa radigm and compare it against strong state. Pure distortion measur es the average gap between the actual value of the state and the value maintained at a remote node. On the other hand, the use o f confidence increases the protocol’s ability to cope with eve n large pure distortion. The resulting effective distortion is cap tured by the informed distortion metric. Using mathematical analysis, we compare weak with strong state. Local updates reduce the pure distortion because the protocol uses the best estimate of state value. The informed distortion is also significantly less because the probabili stic confidence value hints the protocol if the state is invalid. T he weak state mechanism can be used to build protocols (eg: WSR [1]), which systematically interpret the state information. The state itself can be mostly updated locally, with less frequent exp licit update messages over the network (i.e. leading to dramatic reductions in control traffic).
-
Cross-Layer Optimal Policies for Spatial Diversity Relaying in Mobile Ad Hoc Networks.IEEE Transactions on Wireless Communications, 7(8):2930–2939, August 2008.
Abstract
In order to adapt to time-varying wireless channels, various channel-adaptive schemes have been proposed to exploitinherent spatial diversity in mobile/wireless ad hoc networkswhere there are usually alternate next-hop relays availableat a given forwarding node. However, current schemes alongthis line are designed based on heuristics, implying room for performance enhancement. To seek a theoretical foundation for improving spatial diversity gain, we formulate the selection ofthe next-hop as a sequential decision problem and proposea general “Optimal Stopping Relaying (OSR)” framework fordesigning such next-hop diversity schemes. As a particularexample, assuming Rayleigh fading channels, we implement anOSR strategy to optimize information efficiency (IE) in a protocolstack consisting of Greedy Perimeter Stateless Routing (GPSR)and IEEE 802.11 MAC protocols. We present mathematicalanalysis of the proposed OSR together with other strategies inliterature for a single forwarding node. In addition, we performextensive simulations (using QualNet) to evaluate the end-to-endperformance of these relaying strategies in a multi-hop network.Both the mathematical and simulation results demonstrate thesuperiority of OSR over other existing schemes. -
Link State Routing Overhead in Mobile Ad Hoc Networks: A Rate-Distortion Formulation.IEEE INFOCOM 2008, Phoenix, AZ, April 2008.
Abstract
In this paper an information-theoretic formulation is used for characterizing the minimum overhead of maintaining link state information across a mobile ad hoc network. The minimum overhead problem is formulated a rate-distortion problem. Lower bounds are derived for the minimum overhead incurred by maintaining link state information when link state routing protocols are designed with guaranteed delivery ratio for data packets. The deficit caused by the this overhead on the overall transport capacity of a mobile network is characterized. Further a threshold value is derived for the delivery error ratio, and it is shown that no link state routing protocol can achieve a delivery error ratio smaller than this threshold. -
Optimal Location Updates in Mobile Ad Hoc Networks: A Separable Cost Case.IEEE GLOBECOM 2008, New Orleans, LA, December 2008.
Abstract
We consider the location service in a mobile ad-hoc network (MANET), where each node needs to maintain its location information by 1) frequently updating its location information within its neighboring region, which is called neighborhood update (NU), and 2) occasionally updating its location information to certain distributed location server in the network, which is called location server update (LSU). The trade off between the operation costs in location updates and the performance losses of the target application due to location inaccuracies (i.e., application costs) imposes a crucial question for nodes to decide the optimal strategy to update their location information, where the optimality is in the sense of minimizing the overall costs. In this paper, we develop a stochastic sequential decision framework to analyze this problem. Under a Markovian mobility model, the location update decision problem is modeled as a Markov Decision Process (MDP). We first investigate the monotonicity properties of optimal NU and LSU operations with respect to location inaccuracies under a general cost setting. Then, given a separable cost structure, we show that the location update decisions of NU and LSU can be independently carried out without loss of optimality, i.e., a separation property. From the discovered separation property of the problem structure and the monotonicity properties of optimal actions, we find that 1) there always exists asimple optimal threshold -based update rule for LSU operations; 2) for NU operations, an optimal threshold-based update rule exists in a low-mobility scenario. In the case that no a priori knowledge of the MDP model is available, we also introduce a practical model-freelearning approach to find a near-optimal solution for the problem. -
A Unified Model for Joint Throughput-Overhead Analysis of Mobile Ad Hoc Networks. Selected Among 3 Best Papers11th ACM International Symposium on Modeling, Analysis and Simulation of Wireless and Mobile Systems (MSWiM 2008), Vancouver, BC, October 2008.
-
Stochastic Event Capture Using Mobile Sensors Subject to a Quality Metric.IEEE Transactions on Robotics, 23(4):676–692, August 2007.
Abstract
Mobile sensors cover more area over a period of time than the same number of stationary sensors. However, the quality of coverage achieved by mobile sensors depends on the velocity, mobility pattern, number of mobile sensors deployed and the dynamics of the phenomenon being sensed. The gains attained by mobile sensors over static sensors and the optimal motion strategies for mobile sensors are not well understood. In this paper we consider the problem of event capture using mobile sensors. The events of interest arrive at certain points in the sensor field and fade away according to arrival and departure time distributions. An event is said to be captured if it is sensed by one of the mobile sensors before it fades away. For this scenario we analyze how the quality of coverage scales with the velocity, path and number of mobile sensors. We characterize the cases where the deployment of mobile sensors has no advantage over static sensors and find the optimal velocity pattern that a mobile sensor should adopt. We also present algorithms for two motion planning problems: (i) for a single sensor, what is the minimum speed and sensor trajectory required to satisfy a bound on event loss probability and (ii) for sensors with fixed speed, what is the minimum number of sensors required to satisfy a bound on event loss probability. When events occur only along a line or a closed curve our algorithms return optimal velocity for the minimum velocity problem. For the minimum sensor problem, the number of sensors used is within a factor two of the optimal solution. For the case where the events occur at arbitrary points on a plane we present heuristic algorithms for the above motion planning problems and bound their performance with respect to the optimal. The results of this paper have wide range of applications in areas like surveillance, wildlife monitoring, hybrid sensor networks and under-water sensor networks. -
Optimizing Random Walk Search Algorithms in P2P Networks.Computer Networks, 51(6):1499–1514, April 2007.
Abstract
In this paper we develop a model for random walk-based search mechanisms in unstructured P2P networks. This model is used to obtain analytical expressions for the performance metrics of random walk search in terms of the popularity of the resource being searched for and the random walk parameters. We propose an equation-based adaptive search mechanism that uses an estimate of the popularity of a resource in order to choose the parameters of random walk such that a targeted performance level is achieved by the search. We also propose a low-overhead method for maintaining an estimate of popularity that utilizes feedback (or lack there-off) obtained from previous searches. Simulation results show that the performance of the equation-based adaptive search is significantly better than the non-adaptive random walk and other straight-forward adaptive mechanisms -
Optimal Policies for Distributed Data Aggregation in Wireless Sensor Networks.IEEE INFOCOM 2007, Anchorage, AK, May 2007.
Abstract
We consider the scenario of distributed data aggregation in wireless sensor networks, where each sensor can obtain and estimate the information of the whole sensing field through local data exchange and aggregation. The intrinsic trade-off between energy and delay in aggregation operations imposes a crucial question on nodes to decide optimal instants for forwarding their samples. The samples could be composed of the information from their own sensor readings or an aggregation of information with other samples forwarded from neighboring nodes. By considering the randomness of the sample arrival instants and the uncertainty of the availability of the multiaccess communication channel due to the asynchronous nature of information exchange among neighboring nodes, we propose a decision process model to analyze this problem and determine the optimal decision policies at nodes with local information. We show that, once the statistics of the sample arrival and the availability of the channel satisfy certain conditions, there exist optimal control-limit type policies which are easy to implement in practice. In the case that the required conditions are not satisfied, we provide two learning algorithms to solve a finite-state approximation model of the decision problem. Simulations on a practical distributed data aggregation scenario demonstrate the effectiveness of the developed policies, which can also achieve a desired energy-delay tradeoff. -
Capacity Deficit in Mobile Wireless Ad Hoc Networks Due to Geographic Routing Overheads.IEEE INFOCOM 2007, Anchorage, AK, May 2007.
Abstract
Overheads incurred by routing protocols diminish the capacity available for relaying useful data over a mobile wireless ad hoc network. Discovering and understanding the lower bounds on the amount of protocol overhead incurred for routing data packets is important for development of efficient routing protocols, and for understanding the actual (effective) capacity available for network users. In this paper we use an information-theoretic approach for characterizing the minimum routing overheads of geographic routing in a mobile network. We formulate the minimum overhead problem as a rate-distortion problem. The formulation may be applied to networks with arbitrary traffic arrival and location service schemes. We evaluate lower bounds on the minimum overheads incurred for maintaining the location of destination nodes and consistent neighborhood information in terms of node mobility and packet arrival process. We also characterize the deficit caused by the routing overheads in the overall transport capacity of a mobile network. -
Weak State Routing for Large Scale Dynamic Networks.ACM MobiCom 2007, Montreal, QC, Canada, September 2007.
Abstract
Routing in communication networks involves the indirection from a persistent name (or ID) to a locator and delivering packets based upon the locator. In a large-scale, highly dynamic network, the ID-to-locator mappings are both large in number, and change often. Traditional routing protocols require high overhead to keep these indirections up-to-date. In this paper, we propose Weak State Routing (WSR), a routing mechanism for large-scale highly dynamic networks. WSR's novelty is that it uses random directional walks biased occasionally by weak indirection state information in intermediate nodes. The indirection state information is weak, i.e. interpreted not as absolute truth, but as probabilistic hints. Nodes only have partial information about the region a destination node is likely to be. This method allows us to aggregate information about a number of remote locations in a geographic region. In other words, the state information maps a set-of-IDs to a geographical region. The intermediate nodes receiving the random walk use a method similar to longest-prefix-match in order to prioritize their mappings to decide how to bias and forward the random walk. WSR can also be viewed as an unstructured distributed hashing technique. WSR displays good rare-object recall with scalability properties similar to structured DHTs, albeit with more tolerance to dynamism and without constraining the degree distribution of the underlying network. Through simulations, we show that WSR offers a high packet delivery ratio, more than 98%. The control packet overhead incurred in the network scales as O(N) for N-node networks. The number of mappings stored in the network appears to scale as $\Theta(N^{3/2})$. We compare WSR with Dynamic Source Routing (DSR) and geographic forwarding (GPSR) combined with Grid Location Service (GLS). Our results indicate that WSR delivers more packets with less overhead at the cost of increased path length. -
Delay and Capacity in Energy Efficient Sensor Networks.Fourth ACM/SIGMOBILE International Workshop on Performance Evaluation of Wireless Ad Hoc, Sensor, and Ubiquitous Networks (PE-WASUN 2007), Chania, Greece, October 2007.
Abstract
MAC protocols for wireless sensor networks employ periodic switching to low energy sleep state in order to enhance network lifetime. During the sleep state, the sensors do not perform energy consuming operations such as receiving and transmitting packets. During the normal state, CSMA based multi-access mechanism is the MAC protocol of choice in distributed, unsynchronized sensor networks. The energy conserving mechanism has a two-fold effect on delay in the network. On one hand it increases delay since many a times the intended receiver may be in sleep state and the transmitter has to delay the transmission to allow the receiver to wake up. On the other hand, since the sensors do not transmit in sleep state, the contention for channel is reduced which tends to improve delay. In this paper we present a queuing theoretic analysis of delay and capacity in sensor networks with uncoordinated sleep mechanism and characterize the energy-delay-capacity tradeoffs. We consider several sleep states which consume different levels of energy. We model sensor networks as queuing networks and evaluate closed form expressions for average packet delay and maximum achievable pernode throughput in terms of network parameters and sleep schedule. Comparisons with the performance of networks that do not employ any energy conserving mechanisms show that any of the energy conserving sleep states in the networks considered in this paper leads to considerable degradation in delay and capacity of the network.
-
Coverage by Directional Sensors in Randomly Deployed Wireless Sensor Networks.Journal of Combinatorial Optimization, Special Issue on Network Applications, 11(1):21–41, February 2006.
Abstract
We study a novel 'coverage by directional sensors' problem with tunable orientations on a set of discrete targets. We propose a maximum coverage with minimum sensors (MCMS) problem in which coverage in terms of the number of targets to be covered is maximized whereas the number of sensors to be activated is minimized. We present its exact integer linear programming (ILP) formulation and an approximate (but computationally efficient) centralized greedy algorithm (CGA) solution. These centralized solutions are used as baselines for comparison. Then we provide a distributed greedy algorithm (DGA) solution. By incorporating a measure of the sensors residual energy into DGA, we further develop a sensing neighborhood cooperative sleeping (SNCS) protocol which performs adaptive scheduling on a larger time scale. Finally, we evaluate the properties of the proposed solutions and protocols in terms of providing coverage and maximizing network lifetime through extensive simulations. Moreover, for the case of circular coverage, we compare against the best known existing coverage algorithm -
Error Resilient Image Transport in Wireless Sensor Networks.Computer Networks, 50(15):2873–2887, October 2006.
Abstract
In this paper, we propose an 'in-network' diversity combining scheme for image transport over wireless sensor networks. We consider a wireless sensor network with both wireless link impairments and node failures. We analyze two performance metrics of the proposed image transport scheme: energy consumption and received image quality distortion. Our analysis models key aspects of the network including forward error correction, path diversity, and the multi-hop nature of ad-hoc networks. The channel model used is a two-state Markov model describing errors on the bit level. We also use a two-state Markov model of node transitions between an 'on' and 'off' state. Reed-Solomon coding is used for forward error correction. Theoretical and simulation results show the robustness improvement. This work also helps in understanding the tradeoffs between image quality distortion and energy consumption as a function of various network parameters such as the number of hops between the source and the destination, the average channel error rate, and the average node failure rate. [All rights reserved Elsevier] -
Stochastic Event Capture Using Mobile Sensors Subject to a Quality Metric.ACM MobiCom 2006, Los Angeles, CA, September 2006.
Abstract
Mobile sensors cover more area over a period of time than the same number of stationary sensors. However, the quality of coverage achieved by mobile sensors depends on the velocity, mobility pattern, number of mobile sensors deployed and the dynamics of the phenomenon being sensed. The gains attained by mobile sensors over static sensors and the optimal motion strategies for mobile sensors are not well understood. In this paper we consider the problem of event capture using mobile sensors. The events of interest arrive at certain points in the sensor field and fade away according to arrival and departure time distributions. An event is said to be captured if it is sensed by one of the mobile sensors before it fades away. For this scenario we analyze how the quality of coverage scales with the velocity, path and number of mobile sensors. We characterize the cases where the deployment of mobile sensors has no advantage over static sensors and find the optimal velocity pattern that a mobile sensor should adopt. We also present algorithms for two motion planning problems: (i) for a single sensor, what is the minimum speed and sensor trajectory required to satisfy a bound on event loss probability and (ii) for sensors with fixed speed, what is the minimum number of sensors required to satisfy a bound on event loss probability. When events occur only along a line or a closed curve our algorithms return optimal velocity for the minimum velocity problem. For the minimum sensor problem, the number of sensors used is within a factor two of the optimal solution. For the case where the events occur at arbitrary points on a plane we present heuristic algorithms for the above motion planning problems and bound their performance with respect to the optimal. The results of this paper have wide range of applications in areas like surveillance, wildlife monitoring, hybrid sensor networks and under-water sensor networks. -
Load Balanced Link Reversal Routing in Mobile Wireless Ad Hoc Networks.4th Asian International Mobile Computing Conference (AMOC 2006), Kolkata, India, January 2006.
Abstract
Link reversal routing (LRR) is a local, distributed, and low-overhead technique used to maintain loop free routes in mobile wireless ad hoc networks. We explore the problem of load balancing the packet traffic in the network when using the LRR created routes. We study a fundamental LRR algorithm and identify usual situations which cause the load to be unbalanced. We propose three modifications to the LRR algorithm such that the load is distributed in a more uniform manner. The modifications preserve all the desirable qualities of LRR algorithms such as loop free routes, local response to topology change, low overhead and are completely distributed in nature. We perform simulations in order to evaluate the performance of the proposed modifications for both single-path and multi-path scenarios. The simulation results show that the modifications enable LRR to provide a much improved load balancing and ensure higher network lifetime. -
Energy-Efficient Connected Coverage in Wireless Sensor Networks.4th Asian International Mobile Computing Conference (AMOC 2006), Kolkata, India, January 2006.
Abstract
. -
Coverage by Directional Sensors.4th International Symposium on Modeling and Optimization in Mobile, Ad Hoc and Wireless Networks (WiOpt 2006), Boston, MA, April 2006.
Abstract
In this paper, we study a novel coverage by directional sensors problem with tunable orientations on a set of discrete targets. We propose a Maximum Coverage with Minimum Sensors (MCMS) problem in which coverage in terms of the number of targets to be covered is maximized whereas the number of sensors to be activated is minimized. We present its exact Integer Linear Programming (ILP) formulation and an approximate (but computationally efficient) centralized greedy algorithm (CGA) solution. These centralized solutions are used as baselines for comparison. Then we provide a distributed greedy algorithm (DGA) solution. By incorporating a measure of the sensors residual energy into DGA, we further develop a Sensing Neighborhood Cooperative Sleeping (SNCS) protocol which performs adaptive scheduling on a larger time scale. Finally we evaluate the proposed solutions and protocol in terms of providing coverage and maximizing network lifetime through extensive simulations. -
Cross-Layer Optimal Decision Policies for Spatial Diversity Forwarding in Wireless Ad Hoc Networks.IEEE International Conference on Mobile Ad-Hoc and Sensor Systems (MASS 2006), Vancouver, Canada, October 2006.
Abstract
In order to adapt to the time-varying nature of wireless channels, various channel-adaptive schemes have been proposed to exploit inherent spatial diversity in wireless ad hoc networks where there are usually alternate forwarding nodes available at a given forwarding node. However, existing schemes along this line are designed based on heuristics, implying room for performance enhancement. Thereby, to seek a theoretical foundation for improving spatial diversity gain, we formulate the selection of the next-hop relay as a sequential decision problem and derive a general 'optimal stopping relaying (OSR)' framework for designing such spatial-diversity schemes. As a particular example, assuming Rayleigh fading channels, we implement an OSR strategy to optimize information efficiency (IE) in a protocol stack consisting of greedy perimeter stateless routing (GPSR) and IEEE 802.11 MAC protocols. We present an analysis of the algorithm for a single node. In addition, we perform extensive simulations (using QualNet) to evaluate the end-to-end performance of the proposed forwarding strategy. The results demonstrate the superiority of OSR over other existing schemes -
Queuing Network Models for Delay Analysis of Multihop Wireless Ad Hoc Networks.International Wireless Communications and Mobile Computing Conference (IWCMC 2006), Vancouver, Canada, July 2006.
Abstract
In this paper we analyze the average end-to-end delay and maximum achievable per-node throughput in random access multihop wireless ad hoc networks with stationary nodes. We present an analytical model that takes into account the number of nodes, the random packet arrival process, the extent of locality of traffic, and the back off and collision avoidance mechanisms of random access MAC. We model random access multihop wireless networks as open G/G/1 queuing networks and use the diffusion approximation in order to evaluate closed form expressions for the average end-to-end delay. The mean service time of nodes is evaluated and used to obtain the maximum achievable per-node throughput. The analytical results obtained here from the queuing network analysis are discussed with regard to similarities and differences from the well established information-theoretic results on throughput and delay scaling laws in ad hoc networks. We also investigate the extent of deviation of delay and throughput in a real world network from the analytical results presented in this paper. We conduct extensive simulations in order to verify the analytical results and also compare them against NS-2 simulations -
Delay and Throughput in Random Access Wireless Mesh Networks.IEEE International Conference on Communications (ICC 2006), Istanbul, Turkey, June 2006.
Abstract
Wireless mesh networks (WMNs) are emerging as a popular means of providing connectivity to communities in both affluent and poor parts of the world. The presence of backbone mesh routers and the use of multiple channels and interfaces allow mesh networks to have better capacity than infrastructure-less multihop ad hoc networks. In this paper we characterize the average delay and capacity in WMNs that utilize random medium access (MAC).We model residential area WMNs as open G/G/1 queuing networks. The analytical model takes into account the density of the mesh clients and mesh routers, the random packet arrival process, the degree of locality of traffic and the collision avoidance mechanism of random access MAC. The diffusion approximation method is used to obtain closed form expressions for (a) end-to-end packet delay and (b) maximum achievable per-node throughput. The analytical results describe how the performance of WMNs scales with the number of mesh routers and clients. The results obtained from simulations agree closely with the analytical results. For the asymptotic case (as the network size grows indefinitely), we discuss how the results obtained using the proposed queuing network framework compare against previous well known results on asymptotic capacity of infrastructure-less ad hoc networks. -
Rate-Distortion Bounds on Location-Based Routing Protocol Overheads in Mobile Ad Hoc Networks.44th Annual Allerton Conference on Communication, Control, and Computing, Monticello, IL, September 2006.
Abstract
We present an information theoretic analysis of the minimum routing overhead incurred for reliable routing of packets using location-based routing. We formulate the minimum routing overhead problem as a rate-distortion problem and derive a lower bound on the minimum routing overhead incurred. We also characterize the deficit in transport capacity caused by the routing overheads. It is observed that for high mobility and packet arrival rates, the routing overheads may consume the entire capacity of a network. -
Distortion in Lossy Sensor Networks.IEEE SECON 2006 (Abstract/Poster), Reston, VA, September 2006.
-
Queuing Delay and Achievable Throughput in Random Access Wireless Ad Hoc Networks.IEEE International Workshop on Wireless Ad-Hoc and Sensor Networks (IWWAN 2006), New York, NY, June 2006.
Abstract
In this paper we focus on characterizing the average end-to-end delay and maximum achievable per-node throughput in random access multihop wireless ad hoc networks with stationary nodes. We present an analytical model that takes into account the number of nodes, the random packet arrival process, the extent of locality of traffic, and the back off and collision avoidance mechanisms of random access MAC. We model random access multihop wireless networks as open G/G/1 queuing networks and use diffusion approximation to evaluate closed form expressions for the average end-to-end delay. The mean service time of nodes is derived and used to obtain the maximum achievable per-node throughput. The analytical results obtained here from the queuing network analysis are discussed with regard to similarities and differences from the well established information-theoretic results on throughput and delay scaling laws in ad hoc networks. We also investigate the extent of deviation of delay and achievable throughput in a real world network from the analytical results presented in this paper. We perform extensive simulations and verify that the analytical results closely match the results obtained from simulations.
-
The Impact of Traffic Patterns on the Overhead of Reactive Routing Protocols.IEEE Journal on Selected Areas in Communications, Special Issue on Mobile Ad-Hoc Networks, 23(3):547–560, March 2005.
Abstract
This paper presents a mathematical and simulative framework for quantifying the overhead of reactive routing protocols, such as dynamic source routing and ad hoc on-demand distance vector, in wireless variable topology (ad hoc) networks. A model of the routing-layer traffic, in terms of the statistical description of the distance between a source and a destination, is presented. The model is used to study the effect of the traffic on the routing overhead. Two network models are analyzed; a Manhattan grid model for the case of regular node placement, and a Poisson model for the case of random node placement. We focus on situations where the nodes are stationary but unreliable. For each network model, expressions of various components of the routing overhead are derived as a function of the traffic pattern. Results are compared against ns-2 simulations, which corroborate the essential characteristics of the analytical results. One of the key insights that can be drawn from the mathematical results of this paper is that it is possible to design infinitely scalable reactive routing protocols for variable topology networks by judicious engineering of the traffic patterns to satisfy the conditions presented in this paper -
Energy Efficient Distributed Image Compression in Resource-Constrained Multihop Wireless Networks.Computer Communications, 28(14):1658–1668, September 2005.
Abstract
Efficient compression and transmission of images in a resource-constrained multihop wireless network is considered. Distributed image compression is proposed as a means to overcome the computation and/or energy limitation of individual nodes by sharing the processing of tasks. It has the additional benefit of extending the overall lifetime of the network by distributing the computational load among otherwise idle processors. Two design alternatives for energy efficient distributed image compression are proposed and investigated with respect to energy consumption and image quality. Simulation results show that the proposed scheme prolongs the system lifetime at a normalized total energy consumption comparable to the centralized image compression. [All rights reserved Elsevier] -
Routing in Ad Hoc Networks: A Theoretical Framework with Practical Implications.IEEE INFOCOM 2005, Miami, FL, March 2005.
Abstract
In this paper, information theoretic techniques are used to derive analytic expressions for the minimum expected length of control messages exchanged by proactive routing in a two-level hierarchical ad hoc network. Several entropy measures are introduced and used to bound the memory size necessary for the storage of the routing tables. The entropy rates of the topology sequences are used to bound the communication routing overhead-both the interior routing overhead within a cluster and the exterior routing overhead across clusters. A scalability analysis of the routing overheads with regard to the number of nodes and the cluster size is provided under three different network scaling modes. Finally, practical design issues are studied by providing the optimal cluster sizes that asymptotically minimize (i) the memory requirement for each cluster head; (ii) the total control message routing overhead -
Modeling and Analysis of Random Walk Search Algorithms in P2P Networks.IEEE Second International Workshop on Hot Topics in Peer-to-Peer Systems (Hot-P2P 2005), San Diego, CA, July 2005.
Abstract
In this paper we develop a model for random walk search mechanism in unstructured P2P networks. Using the model we obtain analytical expressions for the performance metrics of random walk search in terms of the popularity of the resource being searched for and the parameters of random walk. We propose an equation based adaptive search mechanism that uses estimate of popularity of a resource in order to choose the parameters of random walk such that a targeted performance level is achieved by the search. We also propose a low-overhead method for maintaining an estimate of popularity that utilizes feedback (or lack there-off) obtained from previous searches. Simulation results show that the performance of equation based adaptive search is significantly better than the non-adaptive random walk. -
Error Resilient Image Transport in Wireless Sensor Networks.5th Workshop on Applications and Services in Wireless Networks (ASWN 2005), Paris, France, June–July 2005.
Abstract
In this paper, we propose an 'in-network' diversity combining scheme for image transport over wireless sensor networks. We consider a wireless sensor network with both wireless link impairments and node failures. We analyze two performance metrics of the proposed image transport scheme: energy consumption and received image quality distortion. Our analysis models key aspects of the network including forward error correction, path diversity, and the multi-hop nature of ad-hoc networks. The channel model used is a two-state Markov model describing errors on the bit level. We also use a two-state Markov model of node transitions between an 'on' and 'off' state. Reed-Solomon coding is used for forward error correction. Theoretical and simulation results show the robustness improvement. This work also helps in understanding the tradeoffs between image quality distortion and energy consumption as a function of various network parameters such as the number of hops between the source and the destination, the average channel error rate, and the average node failure rate. [All rights reserved Elsevier] -
Queuing Network Models for Delay Analysis of Multihop Wireless Ad Hoc Networks.ACM MobiHoc 2005 (Abstract/Poster), Urbana-Champaign, IL, May 2005.
Abstract
In this paper we analyze the average end-to-end delay and maximum achievable per-node throughput in random access multihop wireless ad hoc networks with stationary nodes. We present an analytical model that takes into account the number of nodes, the random packet arrival process, the extent of locality of traffic, and the back off and collision avoidance mechanisms of random access MAC. We model random access multihop wireless networks as open G/G/1 queuing networks and use the diffusion approximation in order to evaluate closed form expressions for the average end-to-end delay. The mean service time of nodes is evaluated and used to obtain the maximum achievable per-node throughput. The analytical results obtained here from the queuing network analysis are discussed with regard to similarities and differences from the well established information-theoretic results on throughput and delay scaling laws in ad hoc networks. We also investigate the extent of deviation of delay and throughput in a real world network from the analytical results presented in this paper. We conduct extensive simulations in order to verify the analytical results and also compare them against NS-2 simulations
-
Cluster-Based Routing Overhead in Networks with Unreliable Nodes.IEEE Wireless Communications and Networking Conference (WCNC 2004), Atlanta, GA, March 2004.
Abstract
While several cluster based routing algorithms have been proposed for ad hoc networks, there is a lack of formal mathematical analysis of these algorithms. Specifically, there is no published investigation of the relation between routing overhead on one hand and route request pattern (traffic) on the other. This paper provides a mathematical framework for quantifying the overhead of a cluster-based routing protocol. We explicitly model the application-level traffic in terms of the statistical description of the number of hops between a source and a destination. The network topology is modelled by a regular two-dimensional grid of unreliable nodes, and expressions for various components of the routing overhead are derived. The results show that clustering does not change the traffic requirement for infinite scalability compared to flat protocols, but reduces the overhead by a factor of O(1/M) where M is the cluster size. The analytic results are validated against simulations of random network topologies running a well known (D-hop max-min) clustering algorithm -
Power Aware Image Transmission in Energy Constrained Wireless Networks.9th IEEE Symposium on Computers and Communications (ISCC 2004), Alexandria, Egypt, June–July 2004.
Abstract
We consider transmitting images in a multihop wireless network with the minimal total power consumption while satisfying an end-to-end image quality constraint. Contrary to popular belief, we show that maximum compression before transmission does not always provide minimal energy consumption, especially in the case of dense sensor networks with complex signal processing algorithms. We formulate the minimal energy transmission problem as an optimization problem and present a heuristic algorithm for it. The proposed algorithm selects the optimal image compression parameters to minimize total energy dissipation given the network conditions and image quality constraints. Simulation results show up to 80% reduction in the total power consumption achieved by using the proposed adaptive algorithm compared to nonadaptive algorithms -
Energy Efficient Distributed JPEG2000 Image Compression in Multihop Wireless Networks.4th Workshop on Applications and Services in Wireless Networks (ASWN 2004), Boston, MA, August 2004.
Abstract
The problem of energy efficient image transmission over a resource constrained multi-hop wireless network is considered. Two methods of data exchange in distributed wavelet transform are proposed and investigated with respect to energy consumption and image quality. An energy-balancing distributed JPEG2000 image compression scheme which uses a combination of tiling of images and load balancing by nodes rotation is proposed. Simulation results show that the proposed scheme prolongs the system lifetime by up to 4 times and has a normalized total energy consumption comparable to centralized image compression
-
Comprehensive Performance Analysis of a TCP Session over a Wireless Fading Link with Queuing.IEEE Transactions on Wireless Communications, 2(2):344–356, March 2003.
Abstract
A link model-driven approach toward transmission control protocol (TCP) performance over a wireless link is presented. TCP packet loss behavior is derived from an underlying two-state continuous time Markov model. The approach presented here is (to our knowledge) the first that simultaneously considers (1) variability of the round-trip delay due to buffer queueing; (2) independent and nonindependent (bursty) link errors; (3) TCP packet loss due to both buffer overflow and channel errors; and (4) the two modes of TCP packet loss detection (duplicate acknowledgments and timeouts). The analytical results are validated against simulations using the ns-2 simulator for a wide range of parameters; slow and fast fading links; small and large link bandwidth-delay products. For channels with memory, an empirical rule is presented for categorizing the impact of channel dynamics (fading rate) on TCP performance -
Stochastic Modeling of TCP in Networks with Abrupt Delay Variations.Wireless Networks, 9(5):509–524, September 2003.
Abstract
An analytical model of TCP (Transport Control Protocol) over an end-to-end path with random abrupt round-trip time (RTT) changes is presented. Modeling the RTT as a stochastic process, we analytically quantify and compare between the degree of degradation of the steady-state average throughput and window size due to spurious retransmissions for the different versions of TCP (Reno/NewReno versus Tahoe). The modeling methodology in this paper is used for evaluating different design alternatives for TCP for highly dynamic networks -
A Bluetooth Scatternet Formation Algorithm for Networks with Heterogeneous Device Capabilities.Lecture Notes in Computer Science: Information Networking, 2662:295–305, 2003.
Abstract
This paper focuses on Bluetooth, a promising new wireless technology, developed mainly as a cable replacement. We argue that, in practice, Bluetooth devices will have different power capabilities, classifying them as either high-power or low-power nodes. We propose a deterministic, distributed algorithm that accounts for the physical properties of devices, connecting nodes into a scatternet of small diameter. The proposed protocol results in a high effective throughput and allows components to arrive and leave arbitrarily, dynamically updating the cluster formation. Performance is evaluated through extensive ns-2 simulations. -
Information-Theoretic Bounds for Mobile Ad-Hoc Networks Routing Protocols.Lecture Notes in Computer Science: Information Networking, 2662:651–661, 2003.
Abstract
In this paper, we define the routing overhead as the amount of information needed to describe the changes in a network topology. We derive a universal lower bound on the routing overhead in a mobile ad-hoc network. We also consider a prediction-based routing protocol that attempts to minimize the routing overhead by predicting the changes in the network topology from the previous mobility pattern of the nodes.We apply our approach to a mobile ad-hoc network that employs a dynamic clustering algorithm, and derive the optimal cluster size that minimizes the routing overhead, with and without mobility prediction. We believe that this work is a fundamental and essential step towards the rigorous modeling, design and performance comparisons of protocols for ad-hoc wireless networks by providing a universal reference performance curve against which the overhead of different routing protocols can be compared. -
Reactive Routing Overhead in Networks with Unreliable Nodes.ACM MobiCom 2003, San Diego, CA, September 2003.
Abstract
This paper presents a new mathematical and simulative framework for quantifying the overhead of a broad class of reactive routing protocols, such as DSR and AODV, in wireless variable topology (ad-hoc) networks. We focus on situations where the nodes are stationary but unreliable, as is common in the case of sensor networks. We explicitly model the application-level traffic in terms of the statistical description of the number of hops between a source and a destination. The sensor network is modelled by an unreliable regular Manhattan (i.e. degree four) grid, and expressions for various components of the routing overhead are derived. Results are compared against ns-2 simulations for regular and random topologies, which corroborate the essential characteristics of the analytical results. One of the key insights that can be drawn from the mathematical results of this paper is that it is possible to design infinitely scalable reactive routing protocols for variable topology networks by judicious engineering of the traffic patterns to satisfy the conditions presented in this paper. -
A Bluetooth Scatternet Formation Algorithm for Networks with Heterogeneous Device Capabilities.International Conference on Networks (ICOIN 2003), Jeju Island, Korea, February 2003.
Abstract
This paper focuses on Bluetooth, a promising new wireless technology, developed mainly as a cable replacement. We argue that, in practice, Bluetooth devices will have different power capabilities, classifying them as either high-power or low-power nodes. We propose a deterministic, distributed algorithm that accounts for the physical properties of devices, connecting nodes into a scatternet of small diameter. The proposed protocol results in a high effective throughput and allows components to arrive and leave arbitrarily, dynamically updating the cluster formation. Performance is evaluated through extensive ns-2 simulations. -
Information-Theoretic Bounds for Mobile Ad-Hoc Networks Routing Protocols. Nominated for Best Paper AwardInternational Conference on Networks (ICOIN 2003), Jeju Island, Korea, February 2003.
-
Information-Theoretic Lower Bounds on the Routing Overhead in Mobile Ad-Hoc Networks.IEEE International Symposium on Information Theory (ISIT 2003), Yokohama, Japan, June 2003.
Abstract
In coding theory, a channel coding algorithm is good if it achieves the Shannon capacity [1]. Similarly, we seek to derive a universal curve against which we can measure how good (or bad) a variable topology routing protocol (e.g. for ad-hoc networks) performs, in comparison with a theoretical minimum routing overhead, which is the amount of information needed to describe the changes in a dynamic network topology.
-
Modeling Random Early Detection in a Differentiated Services Network.Computer Networks, 40(4):537–556, November 2002.
Abstract
An analytical framework for modeling a network of random early detection (RED) queues with mixed traffic types (e.g. TCP and UDP) is developed. Expressions for the steady-state goodput for each flow and the average queuing delay at each queue are derived. The framework is extended to include a class of RED queues that provides differentiated services for flows with multiple classes. Finally, the analysis is validated against ns simulations for a variety of RED network configurations where it is shown that the analytical results match with those of the simulations within a mean error of 5%. Several new analytical results are obtained; TCP throughput formula for a RED queue; TCP timeout formula for a RED queue and the fairness index for RED and tail drop
-
TCP in Networks with Abrupt Delay Variations and Random Loss.IEEE Military Communications Conference (MILCOM 2001), San Francisco, CA, October 2001.
Abstract
This paper provides a preliminary investigation of the effect of abrupt round-trip variations on the performance of different versions of TCP. It is shown that end-to-end goodput of a bulk TCP transfer can be severely limited by variations in RTT primarily due to the non-adaptiveness of TCP's timeout estimation and fast recovery thresholds. The paper proposes a model for evaluating the performance of TCP in environments with abrupt RTT changes and random packet loss and outlines possible future TCP improvements -
Analytic Understanding of RED Gateways with Multiple Competing TCP Flows.IEEE GLOBECOM 2000, San Francisco, CA, November–December 2000.
Abstract
An analytical framework for multiple TCP flows sharing a bottleneck link under the Random Early Detection (RED) regime is developed. Closed form expressions for the steady state throughput and average queueing delay are derived and verified by simulations; these show that RED significantly improves the inherent TCP bias against links with higher round-trip delays as compared to Tail Drop, contrary to prevailing belief. Further, we derive closed form bounds on the minimum average queuing delay achievable through a RED gateway with no deterministic packet drop. -
Stochastic Modeling of TCP over Lossy Links.IEEE INFOCOM 2000, Tel Aviv, Israel, March 2000.
Abstract
An analytical framework for modeling the performance of a single TCP session in the presence of random packet loss is presented. A Markovian approach is developed that allows us to study both memoryless channels (IID packet loss) and channels with memory (correlated packet loss) modeled by a two-state continuous-time Gilbert model. The analytical results are validated against results using the ns simulator. It is shown that the model predicts throughput for LAN/WAN (low and high bandwidth-delay products) with good accuracy. Further, throughput for the IID loss model is found to be relatively insensitive to the probability density function (PDF) of the loss inter-arrival process. For channels with memory, we present an empirically validated rule of thumb to categorize the channel transition frequency -
Stochastic Modeling of a Single TCP/IP Session over a Random Loss Channel.DIMACS Workshop on Mobile Networks and Computing, Piscataway, NJ, March 1999.
Abstract
In this paper, we present an analytical framework for modeling the performance of a single TCP session in the presence of random packet loss. This framework may be applicable to communications channels that cause random packet loss modelled by appropriate statistics of the inter-loss duration. It is shown that the analytical model predicts the throughput for LANs/WANs (low and high bandwidth-delay products) with reasonable accuracy, as measured against the throughput obtained by simulation. Random loss is found to severely affect the network throughput; higher-speed channels are found to be more vulnerable to random loss than slower channels, especially for moderate to high loss rates. -
Stochastic Modeling of TCP/IP over Random Loss Channels.6th International Conference on High Performance Computing (HiPC 1999), December 1999.
Abstract
An analytical framework for modeling the performance of a single TCP session in the presence of random packet loss is presented that is based on a semi-Markov model for the window size evolution. The model predicts the throughput for LAN/WAN (low and high bandwidth-delay products) with good accuracy, as compared against simulation results with the ns simulator. Generally, higher speed channels are found be more vulnerable to random loss than slower channels, especially for moderate to high loss rates -
Stochastic Modeling of a Single TCP/IP Session over a Random Loss Channel.DIMACS Series in Discrete Mathematics and Theoretical Computer Science: Mobile Networks and Computing. American Mathematical Society, 2000.
Abstract
In this paper, we present an analytical framework for modeling the performance of a single TCP session in the presence of random packet loss. This framework may be applicable to communications channels that cause random packet loss modelled by appropriate statistics of the inter-loss duration. It is shown that the analytical model predicts the throughput for LANs/WANs (low and high bandwidth-delay products) with reasonable accuracy, as measured against the throughput obtained by simulation. Random loss is found to severely affect the network throughput; higher-speed channels are found to be more vulnerable to random loss than slower channels, especially for moderate to high loss rates.
For a complete list see Google Scholar.
Contact
Rensselaer Polytechnic Institute
Troy, New York 12180